Hacked Websites Used in Black Hat SEO Campaign Redirecting Users to Adult Sites
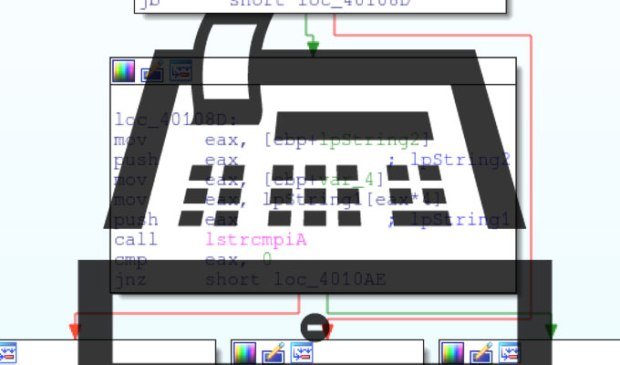
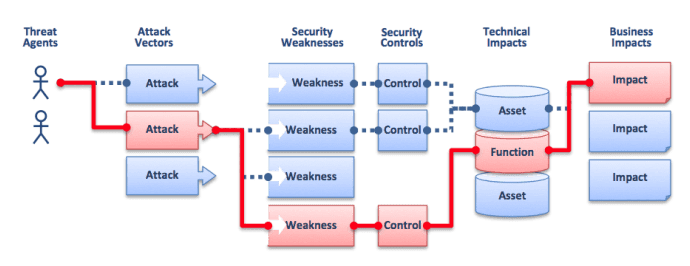
Infected websites are hard to detect, only show up for users coming off search engines and for search bots. A new black hat SEO campaign is leveraging a combination of hackedRead More →