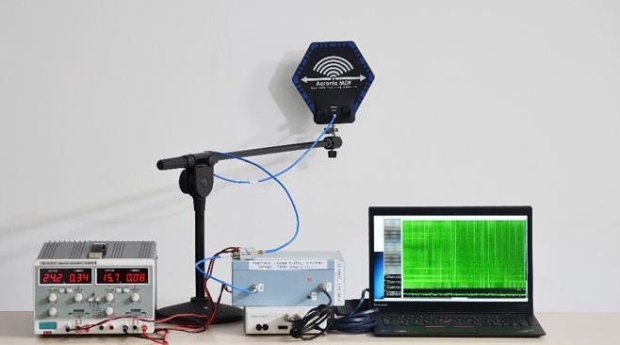
Remotely Disabling a Wireless Burglar Alarm
Countless movies feature hackers remotely turning off security systems in order to infiltrate buildings without being noticed. But how realistic are these depictions? Time to find out. Today we’re releasingRead More →