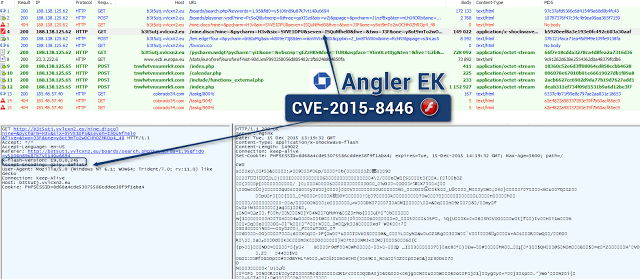
Angler exploit kit includes the code of a recent Flash flaw
A security researcher discovered a new variant of the Angler exploit kit that includes the exploit code for a recently patched Adobe Flash Player flaw. The French security researcher “Kafeine”Read More →