Over the years, I have written many articles here on Null Byte chronicling the many the hacks of the NSA, including the recent hack of the Juniper Networks VPN. (By the way, my speculation in that article has proven to be correct. The NSA did embed a backdoor on those devices.)
Many readers here have expressed surprise, condemnation, and a bit of admiration at the capabilities and tools of the NSA. Much of that is undeserved. The NSA has legal authority to tap resources that none of us do (such as the ISPs and backdoors) as well as supercomputers and other powerful devices that assist them in their hacks. Sometimes, though, the NSA does something innovative and creative. It is one those hacks that I would detail here.
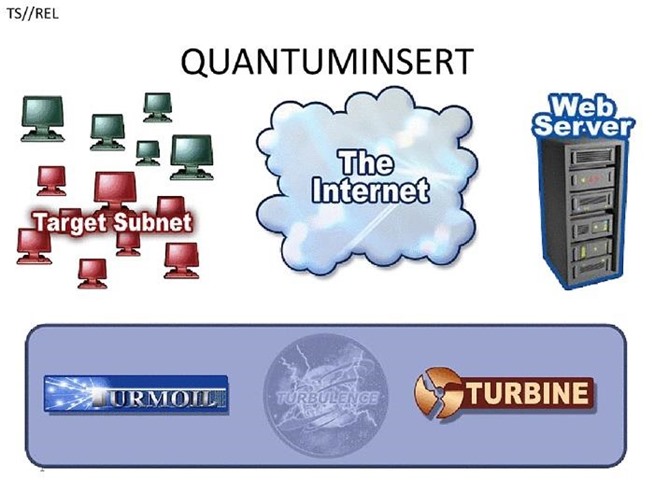
A few years back, specifically 2013, the NSA and GCHQ (Britain’s equivalent agency to the NSA) implemented a hack that came to be known as the “Quantum Insert.” It was used against officials of OPEC and Belgacom (Belgium’s telecom service), and is a variation on classic MitM attacks but with a bit of a twist.
Let’s take a moment to break it down here and see if we could do the same.
Step 1: Monitor/Recon the Target
The first step in the Quantum Insert attack is to monitor/recon the target. The NSA has access to the ISPs and can see all the traffic from the target. From a non-NSA hacker, this would likely require being inside the local area network.
For instance, if we are inside the target’s LAN we may be able to sniff on the target’s network. If we can do that, we can use sniffers such as Tcpdump orWireshark and filter by the target’s IP address. We could automate this process by putting Snort on the LAN and write a rule to see and alert traffic from the target’s IP address. In this way, we could develop a pattern of the target’s web browsing activity.
Step 2: Predict the Target’s Browsing Habits
As we watch the target, we can see the target’s browsing habits. In this way, we can predict what websites that the target is likely to go to each day. In the case of this hack by the NSA, they observed regular traffic to LinkedIn and Slashdot. Based upon what the attacker reconned, they can begin to develop a appropriate hacking strategy.
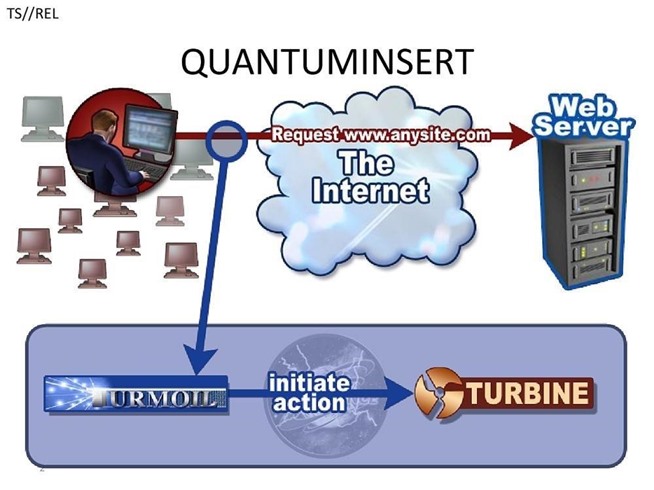
Step 3: Build a Fake Web Server Near the Target
Now that the attacker know what websites the target is likely to visit, they can plan the attack. The key is to “insert” an HTTP reply from our fake website when the target requests the website with a HTTP request.
If we can beat the legitimate website’s reply, the target will get the bogus website. This is often referred to as a “race condition.” If the attacker’s fake HTTP reply arrives at the target before the legitimate reply—if only by a millisecond—the attacker will have won the race and the legitimate reply will be discarded when it arrives. Although the attacker may not win the “race condition” every time, they only need to win once.
Of course, we need a web server and an exact replica of the legitimate website. We can use Apache as our web server and HTTrack to download an exact copy of the website. The closer the proximity of the attacker’s web server is to the target, the faster the HTTP reply will arrive at the target.
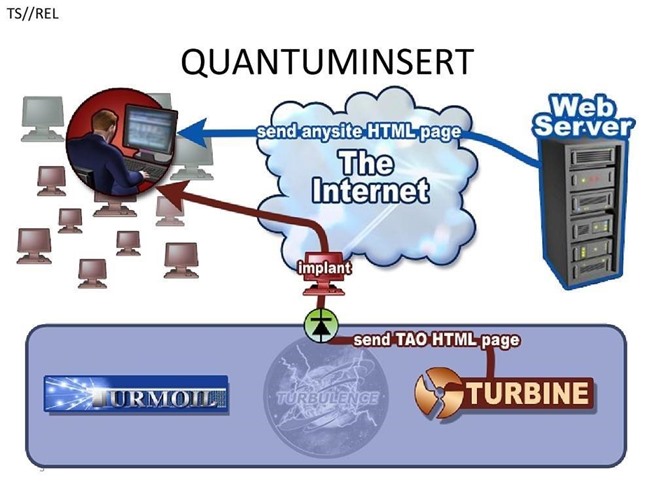
Although the NSA used this race condition, we could also use Dnsspoof to redirect the target’s request to our website, if we are on the local network. The problem with this approach is that a vigilant security admin is likely to see the Dnsspoof packets and the rogue web server on the LAN—but not every security admin is vigilant.
When the bogus webpage arrives, it contains the payload/rootkit that is inserted into the target’s system. As we know, there are numerous Adobe Flash vulnerabilities we can take advantage of as well as almost innumerable browser vulnerabilities. We would have to determine which exploit to use based upon our recon/monitoring in Step #1. For instance, if we determine that the target is using a Firefox browser, we would find a Firefox exploit and embed it in the webpage they request.
Step 4: Own the System!
Now that the NSA/attacker has been able to send the malicious webpage to the target, the rootkit is embedded into the target’s system and the attacker now own’s the target’s system!
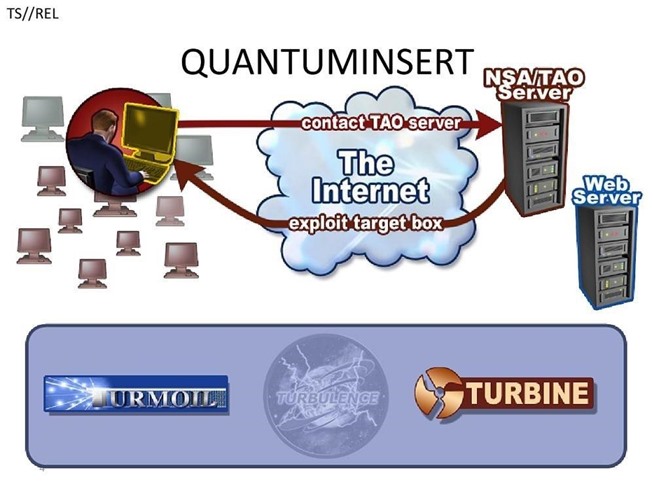
Thanks to WikiLeaks and Edward Snowden for the diagrams. Sometimes we can learn by observing other hackers successful exploits and the NSA is no different.
Keep coming back, my greenhorn hackers, as we develop the most valuable skill set of the 21st century—hacking!
Source:https://null-byte.wonderhowto.com/

Working as a cyber security solutions architect, Alisa focuses on application and network security. Before joining us she held a cyber security researcher positions within a variety of cyber security start-ups. She also experience in different industry domains like finance, healthcare and consumer products.











