A new type of attack would allow a malicious actor to capture the keys pressed on a keyboard using a thermal camera. The discovery was made by pentest experts at the University of California. In simple words, the thermal trace of our fingers over the keyboard can be recorded by a hacker to reveal the user’s passwords or any other text that you typed.
How does it works
According to the pentest specialists in charge of the investigation, if the user types his/her password and then moves away from the keyboard, anyone could learn about this routine.
The attack, known as “Thermonator”, can be used to retrieve user’s sensitive information, such as passwords or short text lines. This attack requires several conditions to function properly. First of all, the attacker must place a special camera with thermal recording capabilities near the victim. The camera should also be able to capture the keys on the victim’s keyboard, otherwise it will not work.
According to the researchers’ explanation of the Thermonator attack, this is an internal attack variant in which an attack scenario proceeds as follows:
- The victim uses a keyboard to enter a valid password as part of the computer’s logon or unlocking procedure.
- Soon after, the victim moves away from his/her workplace.
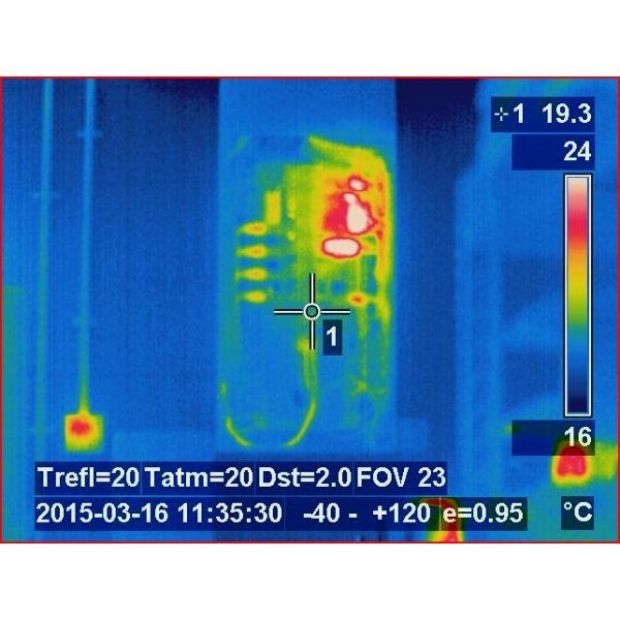
- Using thermal imaging, the attacker collects heat residues on the keyboard.
- The attacker then uses the heat map left by the user to determine the recently pressed keys. This can be done manually (via visual inspection) or automatically (via software).
Once these conditions are fulfilled, the attacker can discover the keys pressed by the victim even without hacking skills. Captured keys can be assembled into possible combinations and can be deployed to perform a dictionary attack, a popular technique for decrypting keys and authentication mechanisms. This is done using hundreds or even millions of possible words.
Pentest specialists conducted several experiments where 31 users entered passwords in four different keyboard models. Then, eight people with a user-level computer domain were asked to get the pressed keys using the recorded data from the thermal camera. The results of these tests revealed that the thermal data recorded up to 30 seconds after text entry is sufficient for a non-professional attacker to retrieve the entire set of keys that the selected user has pressed.
If you are the type of user who presses the keyboard very slowly, you are more susceptible to experiencing the Thermonator attack.
This research exposes the vulnerability of standard password-based systems in front of the possibility of an attack of this nature. Based on the results of the study, information security experts from the International Institute of Cyber Security believe that these attacks represent a considerable threat to this kind of systems, suggesting that it may be time to evaluate passwords as we know them so far.

Working as a cyber security solutions architect, Alisa focuses on application and network security. Before joining us she held a cyber security researcher positions within a variety of cyber security start-ups. She also experience in different industry domains like finance, healthcare and consumer products.