Sonic and ultrasonic signals can be used by attackers to crash hard disk drives, OS. Security researchers from the University of Michigan and Zhejiang University in China have published a new research paper that reveals the latest generation of hard drives are more vulnerable to sonic and ultrasonic signals (inaudible to human) and may lead to crashing operating systems. The sonic and ultrasonic attack could pose as a new attack vector for cybercriminals, wherein regular, built-in speakers or nearby emitters can be used to reach targeted gadget device.
The findings of their study are published in a paper titled [PDF]: ‘Blue Note: How Intentional Acoustic Interference Damages Availability and Integrity in Hard Disk Drives and Operating Systems.” The group presented their research last week in San Francisco at the IEEE Symposium on Security and Privacy.
“Adversaries without special-purpose equipment can cause errors in the hard disk drive using either audible or ultrasonic acoustic waves. Audible waves vibrate the read/write head and platters; ultrasonic waves alter the output of the HDD’s shock sensor, intentionally causing the head to park,” the researchers state in their paper.
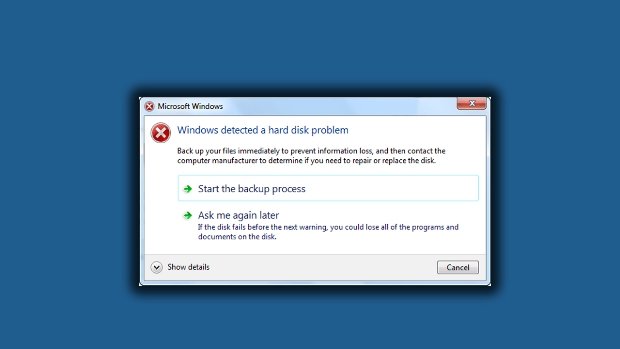
Both of these types of errors can lead to application-level problems or operating system-level, including persistent corruption and system reboots.
“Our experiments show that audible sound causes the head stack assembly to vibrate outside of operational bounds; ultrasonic sound causes false positives in the shock sensor, which is designed to prevent a head crash. The problem poses a challenge for legacy magnetic disks that remain stubbornly common in safety-critical applications such as medical devices and other highly utilized systems difficult to sunset,” the researchers added.
“Intentional acoustic interference causes unusual errors in the mechanics of magnetic hard disk drives in desktop and laptop computers, leading to damage to integrity and availability in both hardware and software such as file system corruption and operating system reboots. An adversary without any special purpose equipment can co-opt built-in speakers or nearby emitters to cause persistent errors.”
According to the researchers, modern mechanical hard drives use shock sensor-driven feed-forward controllers that detect HDD assembly’s head position and enhance the head positioning accuracy while reading and writing the data. However, an attacker by using sonic and ultrasonic sounds can trigger false positives in the shock sensor, which can disrupt the read and write processes of the magnetic hard drive, and damage both the actual drive and corrupt files.
“An adversary can attack a HDD by inducing vibration via acoustic emitters built into the victim system (or a nearby system). In this case, an adversary would temporarily control an emitter in the system though some means. The attack is more likely to succeed when the emitter is powerful and/or very close to the victim,” the study states.
To carry out this kind of attack, the acoustic vibrations must be strong enough and would require accessing nearby speakers or emitters. This obviously presents a challenge, especially for remote attacks. However, the researchers point out that something like this could be accomplished when a victim visits a website or receives a phishing message and reproduces a damaging audio through the system’s speakers.
It’s worth noting that not all built-in speakers are capable of carrying out this sort of attack, although some are, the study states. For instance, the researchers found that in an attack on a PC with a Western Digital Blue WD5000LPVX unit, the unit was exposed to vibrations prompted by a 5 kHz tone at 115.3 dB SPL and a tone from 5 kHz to 117.2 dB SPL. These noise levels are equivalent to the sound of a car horn, live rock music or chainsaw. In another instance, a Dell XPS 15 9550 laptop’s output was measured to be as high as 103 dB SPL from 1 cm away, while writing block signals that occur from signals as low as 95.6 db SPL.
“This demonstrates the possibility of using the laptop’s own speakers to attacks its own hard drive,” the paper states.
While these kind of attacks shouldn’t worry home consumers, as these are typically found in medical devices and CCTV surveillance camera storage, according to the paper. Are businesses and government agencies listening?

Working as a cyber security solutions architect, Alisa focuses on application and network security. Before joining us she held a cyber security researcher positions within a variety of cyber security start-ups. She also experience in different industry domains like finance, healthcare and consumer products.