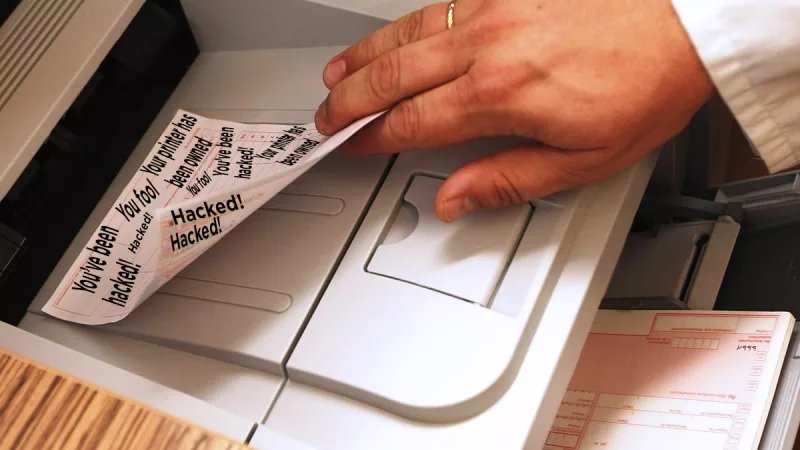
The attackers claim that this time they have compromised hundreds of thousands of devices around the world, in what they themselves called #PrinterHack2
A few days ago, specialists in digital forensics from the International Institute of Cyber Security reported the sudden emergence of a message supporting PiewDiePie, famous YouTuber, in thousands of printers worldwide for the purpose of generating awareness on the security vulnerabilities present in these devices. This time, the hackers claim that they have launched a new attack targeting hundreds of thousands of printers, reprinting a support message to the content creator.
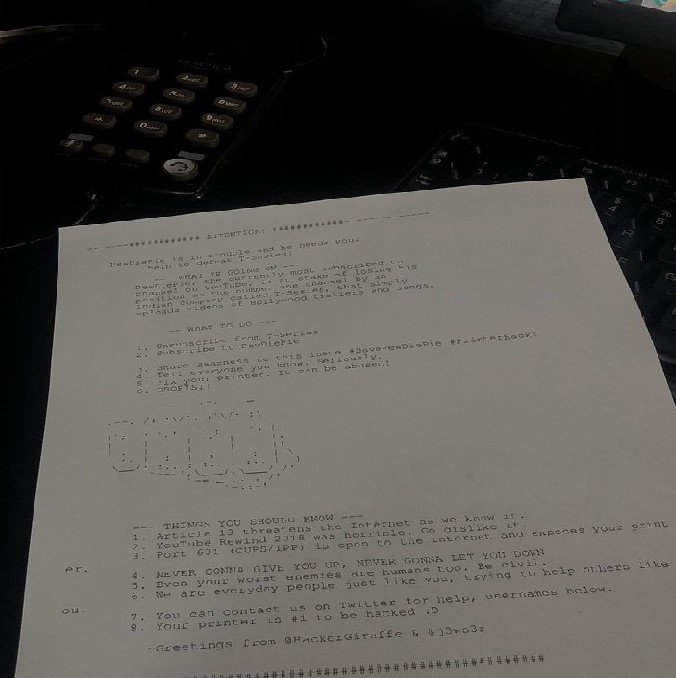
Hackers have been identified themselves on Twitter as TheHackerGiraffe and j3ws3r, and have called this campaign #PrinterHack2.
TheHackerGiraffe claimed through their Twitter account that the number of devices that actually printed this new message was “over 250k printers”, in addition, mentioned that about 2 million IP addresses were used in this second attack campaign.
“Although the actual number of printers affected could vary from our estimates, we can say that the attack affected the IPP, JetDirect and LPD protocols; in addition, we know that 100k printers using the LPD protocol received the message satisfactorily,” TheHackerGiraffe mentioned.
According to specialists in digital forensics, the two hackers who claim to be behind this campaign later stated that they managed to compromised another 100k devices, although this information has not been confirmed yet.
As in the first campaign, the hacked printers showed a message indicating to the user to subscribe to PewDiePie and thus get it to remain as the YouTube channel with more subscribers, since it competes with T-Series channel, dedicated to Indian cinema. Both channels exceed 73 million subscribers.
The first of the alleged victims of the new campaign, based in Argentina, shared via Twitter an image of the message that threw his printer on December 14.
In addition, experts in digital forensics emphasize that these new messages include a description on how port 631 (used for the operation of some printers) is open by default, leaving thousands of computers exposed.
According to the hacker identified as j3ws3r, the goal of this campaign is to raise awareness about the security vulnerabilities present in printers. “Again, our main goal is to highlight the security flaws in the protocols used by these devices”, the hacker mentioned in a tweet.
This campaign has highlighted the multiple security flaws of printers and the possibility of exploitation for access to enterprise networks. In addition, experts in digital forensics had previously discovered a vulnerability that would have made it possible to compromise printers with fax features. Also, a few months ago, the printer manufacturer company Hewlett Packard launched several update patches for hundreds of multifunctional models vulnerable to two remote code execution attacks.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.