The technological giant is in the process of recovering the deleted information
The shut in Azure service last January 29 caused unheard damage. According to network security and ethical hacking experts from the International Institute of Cyber Security, the incident caused the deletion of the databases of some of the users of this service.
The incident affected some Azure SQL databases that use custom KeyVault keys for the Transparent Data Encryption (TDE), according to the incident report received by affected users. Some internal codes accidentally deleted these Azure portal databases, forcing Microsoft to restore customer data from a record stored in the system, although the databases remained offline for five minutes.
According to network security specialists, due to the incident product orders and other data warehouse updates during that five-minute period were lost.
The note received by users explained that the incident occurred automatically while a DNS error was present that blocked access to Microsoft 365 accounts to more than half of the service customers in the cloud: “An automated process designed to enable when custom keys are removed from KeyVault, it caused inadvertent database deletion”.
“We are trying to restore a copy of these databases; the restored databases will be located on the same server as the original database. We ask users to try to identify whether transactions unregistered in this five-minute period could affect their processes or applications outside of the compromised databases”.
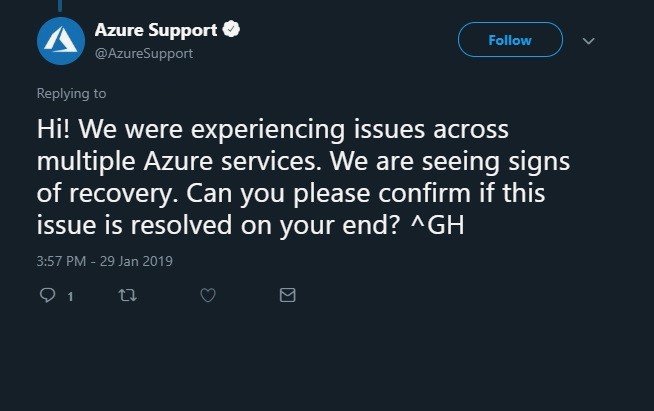
Some affected users have been bothered by this incident on social networks. On Twitter, for example, in the face of multiple user posts reporting Azure’s flaws, the company began responding to tweets with an automated message that briefly describes the incident.
According to network security specialists, Transparent Data Encryption is designed to protect Microsoft Azure’s SQL databases against “multiple malicious activities”; however, this occasion the security measure could not against the malicious script executed during the fall in the Azure service.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











