Although WhatsApp has important security measures, such as end-to-end encryption, this does not mean that the platform is completely secure. A digital forensics specialist has just discovered a vulnerability that, if exploited, allows hackers to access the victim’s files and messages using specially crafted, malicious GIF files.
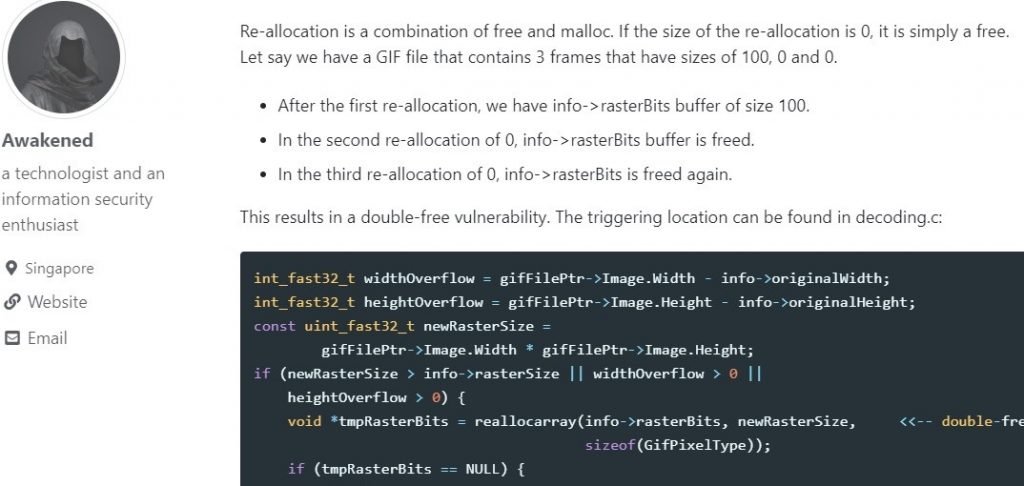
The researcher, known as “Awakened”, mentions that the vulnerability exists due to a “double-free” bug in the instant messaging service. In other words, this is a memory corruption condition that can generate various scenarios, from blocking an app, to generating an attack vector to gain complete access to the targeted device.
According to the digital forensics specialist, all a threat actor requires to trigger this attack is to create a malicious GIF and calmly wait for the victim to access their WhatsApp image gallery. Through GitHub, the specialist mentions that the flaw lies in the implementation of the WhatsApp gallery display, used to generate previews of the files that can be sent through the application.

Apparently, the exploit only works on versions 8.1 and 9.0 of the Android operating system: “Versions 8.0 and earlier are not affected by the flaw”, Awakened mentioned. “It is possible to trigger the bug in version 8.0 and earlier, but the application collapses before it can complete the attack”, adds the researcher.
According to the researcher, Facebook has already received the vulnerability report and started developing a solution. Digital forensics specialists mention that it will be necessary to install the latest WhatsApp update to mitigate the risk of exploitation. Facebook asserts that so far there is no evidence to suggest the exploitation of this flaw in real-world scenarios.
After an apparent confusion inside the team responsible for WhatsApp security, Awakened again contacted the company to clarify some questions about exploiting the vulnerability: “maybe WhatsApp representatives misunderstood the situation,” the expert said. Finally, Awakened sent the company a proof of concept showing all the necessary steps for the exploitation of the flaw. “Facebook addressed the bug, which was fixed in version 2.19.244 of the app,” the specialist concluded.
This is not the first time WhatsApp should fix bugs in its software. According to digital forensics specialists from the International Institute of Cyber Security (IICS) a few months ago a vulnerability was reported in the app that, if exploited, allowed threat actors to inject spying software into the targeted device. The flaw was quickly patched by the company, although it was never specified if there were users affected by the flaw. Recently, a flaw in the messaging service was also discovered that allowed hackers to manipulate the content of a message or even send fake messages. Members of the cybersecurity community are still waiting for new Facebook reports on correcting these bugs.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











