Black Friday sales are about to begin, especially through online stores, although getting carried away with attractive prices on technology devices may not be the best idea. Data protection specialists have continuously pointed out the large number of security flaws in equipment such as smart speakers, tablets, surveillance systems, among others, and an increase in the use of these products would only increase the risk for security of the information of its users.
The security of information and user privacy is vital in the use of smart devices, so below is a list of the 10 devices you should not buy in this holydays.
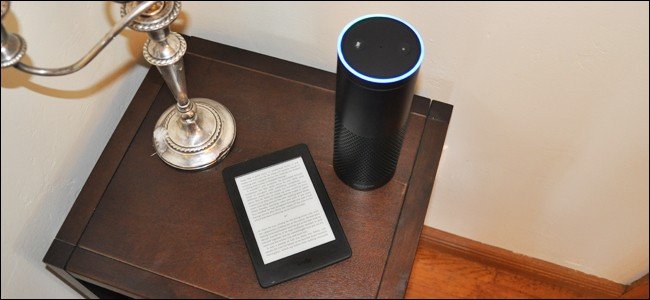
Amazon Echo
A couple of weeks ago, data protection specialists reported that multiple generations of these smart speakers were affected by an old vulnerability that, if exploited, allowed Man-in-The-Middle (MiTM) attacks to be deployed to access networks WPA2 WiFi, so a hacker could access your home network using an Amazon Echo device.
Google Nest
The main use of Google Nest devices is the control of other Internet of Things (IoT) devices; with such extensive access and control, these teams should have the best protections. However, malicious researchers and hackers have demonstrated on multiple occasions how easy it is to compromise these devices, so perhaps the best option is to avoid using them.

Google Home
Of all Google Nest devices the most prominent is Home, the smart speaker that includes the company’s voice assistant. It was recently revealed that Google allows third parties to access some recordings registered by Google Home; the company argues reasons for quality control and the development of the assistant, but this is a clear violation of users’ privacy.

Apple HomePod
This is an integrated speaker with Siri and six powerful smart microphones. Although it offers very good sound quality, data protection specialists are concerned about the high listening capacity of this device. Apple claims that any requests registered by HomePod are encrypted before being sent to its servers, however, other privacy issues may arise in the future.

Ring doorbells
These built-in camera doorbells lack reliable security measures, and even a vulnerability in the software of these devices was discovered that allowed the removal of the name and password of the WiFi network to which they are connected.

Facebook Portal
This smart speaker with screen and webcam was not well received by the public, who still had a recent memory of the Cambridge Analytica privacy scandal. Facebook got to work to try to build trust in Portal; however, the product is still seen as a threat to privacy.

Smart feeders
Xiaomi, in collaboration with Furrytail, launched this year a pet food dispenser operable through an app. While the device caused anticipation, shortly after its release a hacker discovered that limited security measures allowed her to take control of these devices in a really easy way, so it may be better to feed your pet in the traditional way.

Smart Watch for kids
These devices are mainly used to know the location of the child who wears it. However, there are cases where these confidential records are exposed, putting children and even parents at risk, say data protection specialists.

Ring Cameras (indoor and outdoor)
Security deficiencies on these devices could allow malicious users to access the camera software, which could grant them what they need to collect information about victims and even hijack the live feed of these devices.

Link AKC smart collar
This device allows you to know the location of your pet, either via Bluetooth or GPS. Although it seems useful to protect a dog or cat, little is known about its security measures, as the developers do not even specify whether it has encryption. If this protection is not available, the collar may expose the owner’s smart devices.

Data protection specialists from the International Institute of Cyber Security (IICS) ensure that, even though these equipments are constantly updated, security risks also evolve, so it is good that, as regular users of technology, let’s try not to rely entirely on these devices in our everyday lives.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











