Typo squatting is very common among technology users, so threat actors seek to take advantage of these oversights, creating websites of names similar to others by changing only a few characters, to which they hope to redirect unsuspected users, cybersecurity specialists mentioned.
According to a recent report, this practice has been taken a step forward with the discovery of a zero-day vulnerability that uses Latin homoglyph symbols, much like letters, to create malicious and phishing websites.
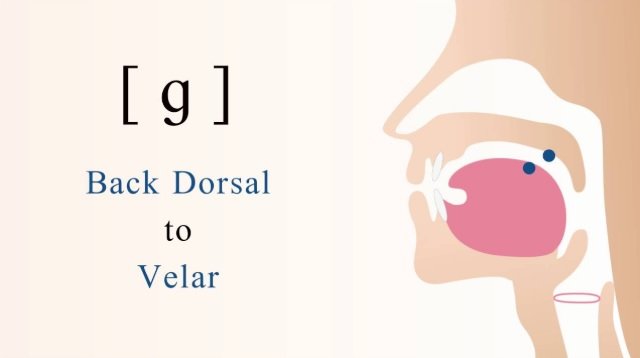
Matt Hamilton, a cybersecurity specialist, published a paper detailing how some homoglyph characters of the Latin International Phonetic Alphabet are used by threat actors for their striking resemblance to common alphabet letters. For example, the symbol of the voiced velar stop is almost the same as the lowercase letter “g”; the Latin letter alpha is very similar to a lowercase “a”, among many other examples.
Cybercriminals take advantage of the resemblance between these characters and the letters of the conventional alphabet to create malicious websites replacing similar letters. For example, a threat actor can register the website “gameplanet.com”, replacing the letter “g” with the symbol of the voiced velar stop; the change is undetectable to the naked eye, so users could easily fall into the trap.
The researcher claims that this variant of attack has been present for years, and has even led various domain providers to think about ways to mitigate this risk, for example by avoiding the use of mixed scripts, excluding the Latin characters and Cyrillic.
In its publication the cybersecurity specialist mentions that, in just over two years of research he has found at least a dozen of these sites that even use active HTTPS certificates, making it even more likely that users with some level of knowledge are victims of the scam.
Due to the potential use of HTTPS certificates, the cybersecurity community reclassified this report, considering it a zero-day flaw that requires all possible security measures. Companies like Google and Amazon are already aware of this risk and plan to counter it.
While this is not a widespread practice in the world of cybercrime, the International Institute of Cyber Security (IICS) considers it necessary to intervene the most important technology companies before this method of attack grows.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











