Phishing 2.0: AI Tools Now Build Fake Login Pages That Fool Even Experts
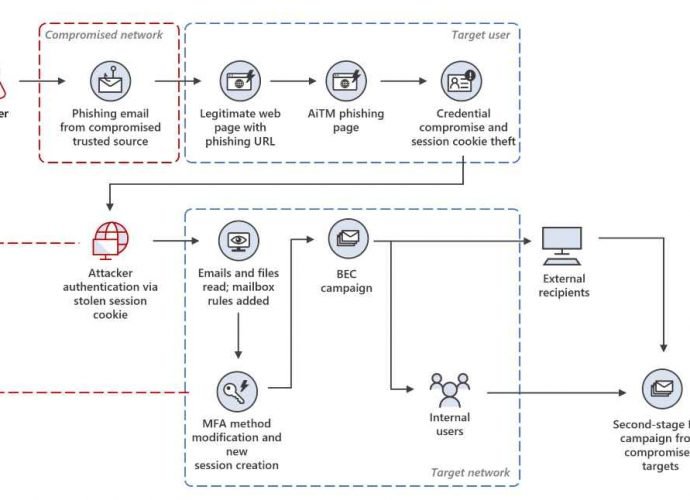
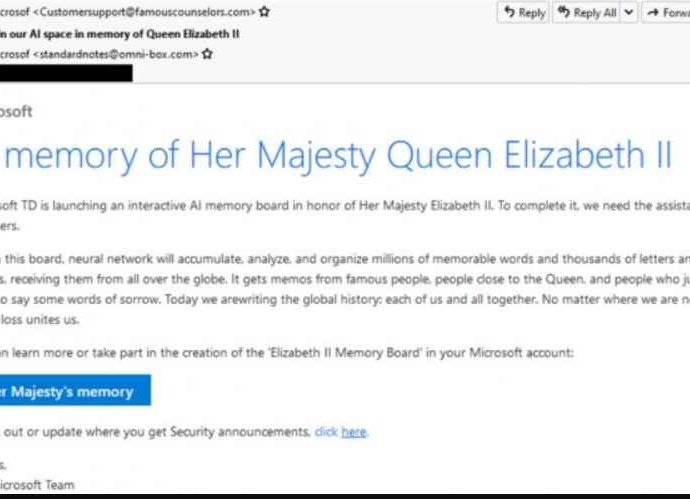
In a recent threat intelligence disclosure, Okta has identified the misuse of Vercel’s v0.dev, a generative AI-powered interface builder, by malicious actors to construct sophisticated phishing websites. These sites areRead More →