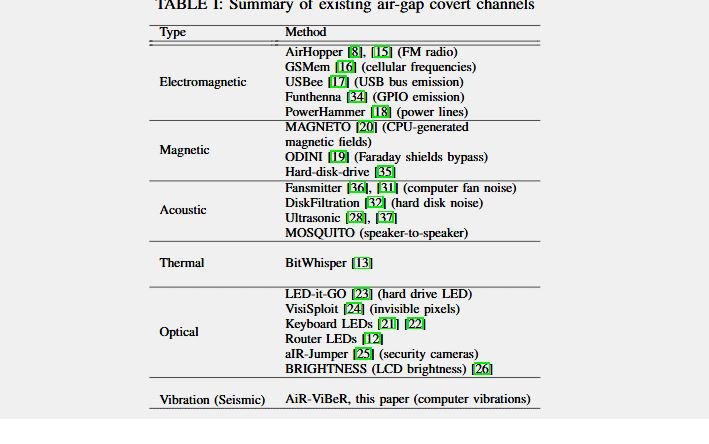
Specialists from a hacking course and members of the computer science department at an Israeli university have published research detailing the use of computer-installed fans to generate controlled vibrations for the purpose of extracting information from complex isolated security systems (known as air-gapped systems).
This method, known as “AiR-ViBeR”, was designed by Mordechai Guri, a specialist at Ben-Gurion University who has previously collaborated in the development of other complex and unconventional methods of data extraction.
These systems are widely used by intelligence agencies, government organizations, and business environments for storing sensitive information. The hacking course specialists claim that this kind of research is essential to know all the possible security risks in the use of these systems.
In his most recent research, Guri decided to focus on a vector never before considered in this field: the vibrations emitted by these systems, specifically the vibrations generated by the fans included in the CPU, GPU, power station fans or any other fan installed on a computer.
The researcher states that it is possible to inject malicious code into an air-gapped system to control the speed at which a fan works; By modifying this function, attack operators could control the frequency of vibrations emitted by these devices and generate a vibration pattern that travels through nearby objects.
The hacking course expert mentions that this attack (which must be launched from a nearby location) can record vibrations produced using accelerometers such as those used by current smartphones to subsequently reconstruct metadata extracted from the security system.
There are two different ways to collect this vibration data:
- A threat actor with physical access to the target network can place multiple smartphones in a location near the air-gapped system
- The attacker can use a variant of malware on employees’ smartphones with access to the target network. This malware should be able to detect these vibrations
It should be noted that this method of data collection is extremely slow (almost 0.5 bits per second), so this could be considered as the least efficient method developed by Guri and his computer. This does not mean that the attack is not feasible, but the possibility of replicating it in a real scenario is very small, as the threat actors behind these kinds of attacks have access to other, much more functional methods.
Finally, the International Institute of Cyber Security (IICS) states that users of these systems should not worry about these attacks, as there are many obstacles to their realization, in addition to other options available to threat actors.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











