Phishing attacks are one of the main threats to technology users. Hackers constantly seek to deceive victims by usurping the name of well-known brands, companies or products, deploying massive campaigns to attract the attention of as many potential victims as possible.
A phishing campaign was recently detected in which threat actors pose as staff from LogMeIn, a popular remote access tool, to extract the credentials of unsuspecting users. Abnormal Security specialists published a report detailing the activity of this hacker group.
The phishing attack campaign was first detected in early May, according to the cybersecurity firm’s report. According to the reports, the need for cybercriminals to impersonate LogMeIn is due to the need to work remotely, so employees of thousands of companies and public organizations must use all available resources to perform their day-to-day work from home.
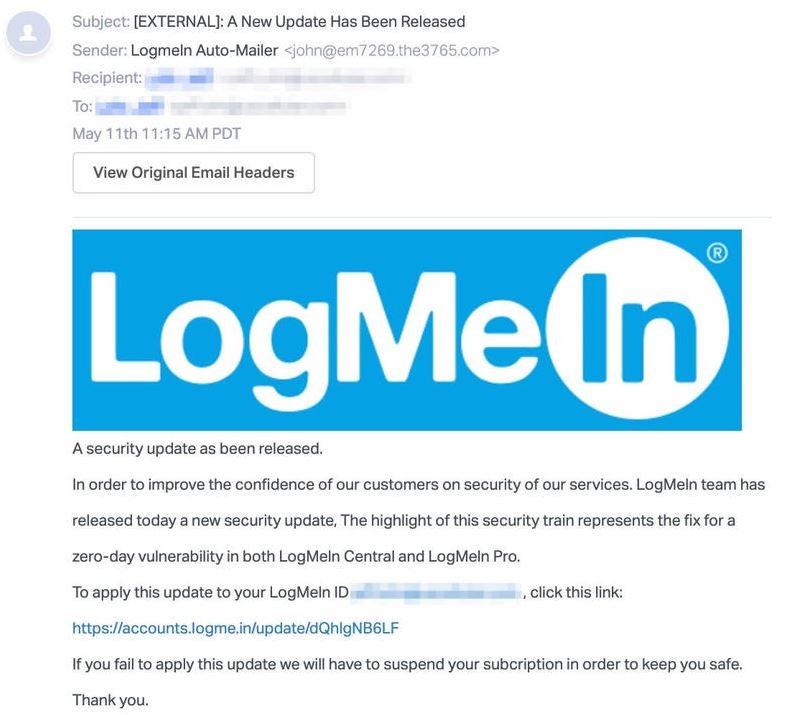
The attack begins with an email purportedly coming from LogMeIn support team, which includes a customer-targeted notice that mentions the release of an update to fix a zero-day vulnerability detected in LogMeIn Central and LogMeIn Pro
Users who would like to install the alleged update patch should click on an attached link, in addition, the email contains a warning that, in case the patch is not installed, the target user’s account will be suspended for exploit prevention purposes. In fact, the link directs users to a fake login page identical to the legitimate LogMeIn site; to give more veracity to this fraudulent site, the campaign operators added images from LastPass, LogMeIn’s parent company.
When victims enter their login credentials on the fake page, this data is sent to the cybercriminals. Because LogMeIn uses a single login method with LastPass, threat actors might try to gain access to the user’s password manager. If this information is accessed, cybercriminals could take control of all victims’ passwords.
Cybersecurity specialists point out that many recently detected cyberattack campaigns have employed similar techniques, as many system administrators or computer tool users seek to keep their deployments always up-to-date. To prevent such attacks, administrators should always verify the provenance of any email, as well as look for information about vulnerabilities and updates on official developer platforms, as well as on organization websites for official disclosure of security flaws.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











