Another day, another security incident reported at Cisco. Vulnerability assessment specialists have revealed the detection of a security breach that affected a sector of your back-end infrastructure. In the announcement, published a few hours ago, the technology company revealed that the threat actors behind the attack exploited a vulnerability in SaltStack, software that Cisco includes with other products to gain access to the following six servers:
- us-1.virl.info
- us-2.virl.info
- us-3.virl.info
- us-4.virl.info
- vsm-us-1.virl.info
- vsm-us-2.virl.info
These six servers provide the back-end infrastructure for VIRL-PE (Internet Routing Lab Personal Edition), a Cisco service that users use to model and create virtual network architectures to test network configurations before deploying computers in real-world scenarios.
Vulnerability assessment experts mention that salt-master servers serving Cisco VIRL-PE versions 1.2 and 1.3 had been compromised. Cisco mentions that patches to fix these bugs had already been released on May 7, along with routine updates for SaltStack software.
It should be noted that the security issue is not located only in the back-end infrastructure. In its report, the company mentions that two of its most popular products also include the SaltSack package, as part of its firmware. Affected products are Cisco VIRL-PE and Cisco Modeling Labs Corporate Edition (CML).
Both VIRL-PE and CML can be used in Cisco-hosted and on-premises scenarios. In case companies use the two products in the same place, Cisco says that CML and VIRL-PE will need to be corrected, mention vulnerability assessment experts. The company today released software updates for both products that incorporate solutions to the two SaltStack vulnerabilities that were used to breach The Cisco VIRL-PE back end.
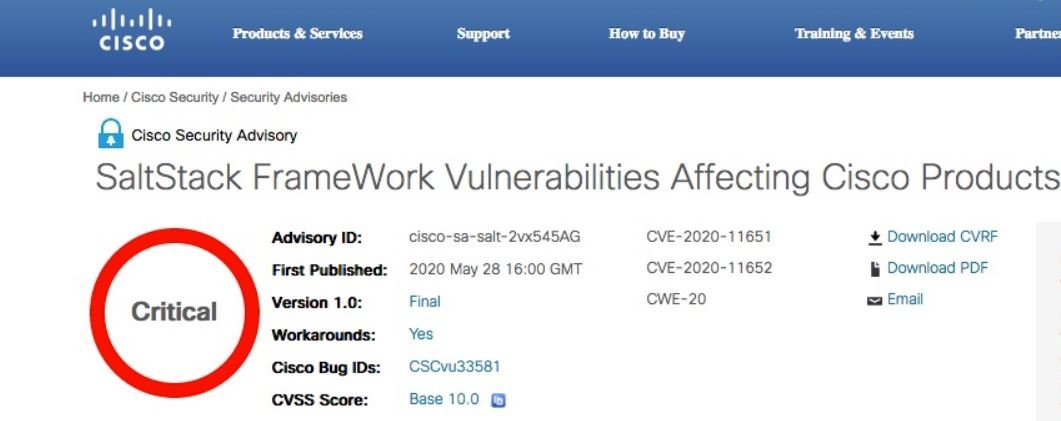
The two failures, identified as CVE-2020-11651 (authentication error) and CVE-2020-11652 (directory escalation) were disclosed to the public on April 30 and were exploited multiple times over the past 30 days. Companies that have reported cases of active exploitation include mobile operating system provider LineageOS, Ghost blog platform, digicert certification authority and search provider Algolia.
In most of these cases, victims mentioned that the hackers compromised SaltStack servers to install cryptocurrency mining malware; So far, Cisco has not added any further details about the attacks. For further reports on vulnerabilities, exploits, malware variants and computer security risks you can access the website of the International Institute of Cyber Security (IICS), as well as the official platforms of technology companies.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











