A web application penetration testing team from tech form Cisco reported a severe vulnerability that could affect at least six of its small business-designed switches. Successful exploiting of the vulnerability would allow unauthenticated remote hackers to access the management interface of affected devices with administrator privileges.
The vulnerability particularly affects Series Smart, Series Managed, and Series Stackable Manager switches. Cisco claims that there are no active exploit reports of this vulnerability, and software updates that correct this flaw are now available to most affected devices. However, some affected switch models have already stopped receiving support from the company.
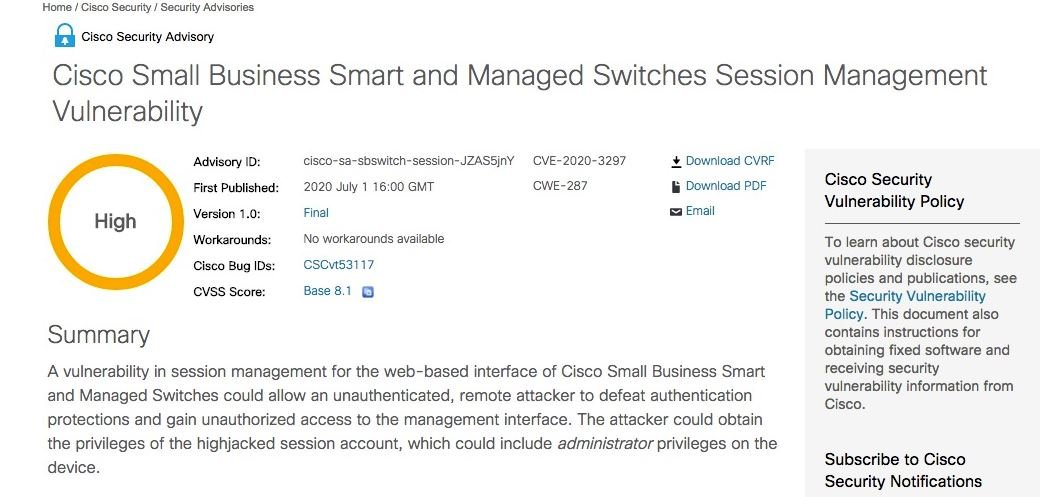
The flaw, tracked as CVE-2020-3297, received a score of 8.1/10 on the Common Vulnerability Scoring System (CVSS) scale, and according to the web application penetration testing experts it exists due to the weak generation of entropy for session ID values. “Threat actors could exploit this vulnerability to determine a current session ID using brute force attacks, reusing the session ID to take control of an ongoing session,” the Cisco alert mentions.
Upon completion of the attack, malicious hackers can bypass the authentication mechanisms implemented on these devices and obtain privileges from the hijacked account. If the affected user has administrator privileges, the hackers could get the highest privileges on the affected system.
Cisco fixed the issue with the release of firmware version 2.5.5.47. This update will apply to Series Smart 250, Series Managed 350 switches, Series Stackable Managed 350X switches, and Series Stackable Managed 550X switches, as mentioned by the web application penetration testing.
Regarding the other affected models, the company announced that they reached the end of their useful life and will not receive updates: “Although these switches are vulnerable, Cisco will not provide a firmware solution,” the company said.
Cisco released Wednesday patches for a number of medium-gravity flaw, including those of its small RV042 and RV-042G routers, its Digital Network Architecture Center, its identity services engine, its Unified Customer Voice Portal, Unified Communications products, and AnyConnect Security Mobility Client. In early June, the network giant also passed three high-gravity flaws in its popular Webex web conferencing application, including one that could allow an unauthenticated attacker to run code remotely on the affected systems.
For further reports on vulnerabilities, exploits, malware variants and computer security risks, it is recommended to enter the website of the International Institute of Cyber Security (IICS), as well as the official platforms of technology companies.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











