Security testing course specialists reported the finding of a vulnerability in PuTTy, an SSH client, Telnet, rlogin, and freely licensed raw TCP. Originally available only for Windows, it is now also available for several Unix platforms and the version for Mac OS Classic and Mac OS X is being developed. Successful exploitation of this vulnerability allows the deployment of Man-in-The-Middle (MiTM) attacks.
Below is a brief description of the reported flaw, in addition to its respective score and tracking key according to the Common Vulnerability Scoring System (CVSS).
Tracked as CVE-2020-14002, this vulnerability exists due to a discrepancy issue in algorithm negotiation, allowing malicious hackers to deploy MiTM attacks. Threat actors can point to initial connection attempts (where the client does not cache any host keys for the server).
The fault received a score of 5.3/10 and resides in the following versions of PuTTY: 0.68, 0.69, 0.70, 0.71, 0.72 & 0.73.
Although the vulnerability can be exploited remotely by unauthenticated hackers, no active exploit attempts have been detected. Security testing course experts have also not detected a useful malware variant to trigger this attack.
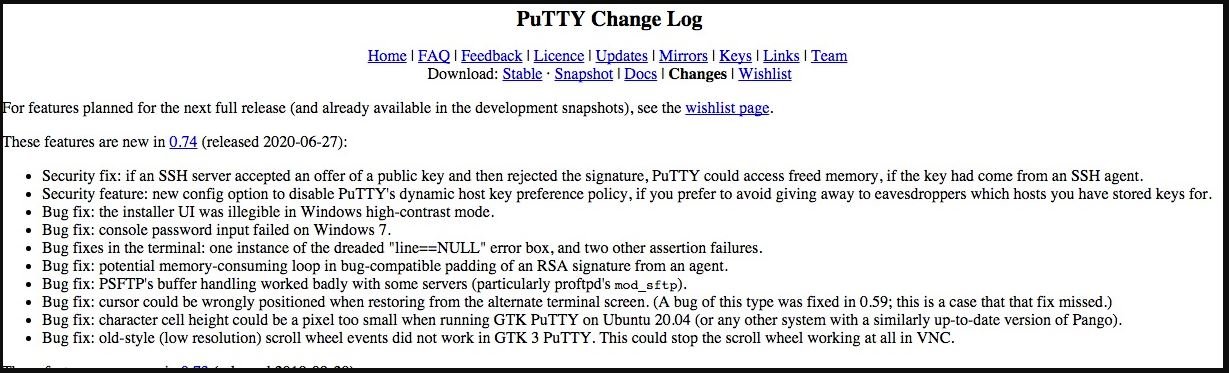
The developers of this tool recognized the report and began preparing the updates. The security patch is now ready, so users of affected deployments are advised to install the fixes below, as for now a workaround is unknown.
For further reports on vulnerabilities, exploits, malware variants and computer security risks, it is recommended to enter the website of the International Institute of Cyber Security (IICS), as well as the official platforms of technology companies.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











