Specialists from a pentesting course company reported the finding of a vulnerability in Python, the popular programming language. According to the report, exploiting this flaw would allow the deployment of denial of service (DoS) attacks.
Below is a brief description of the reported vulnerability, in addition to its respective score and tracking key according to the Common Vulnerability Scoring System (CVSS).
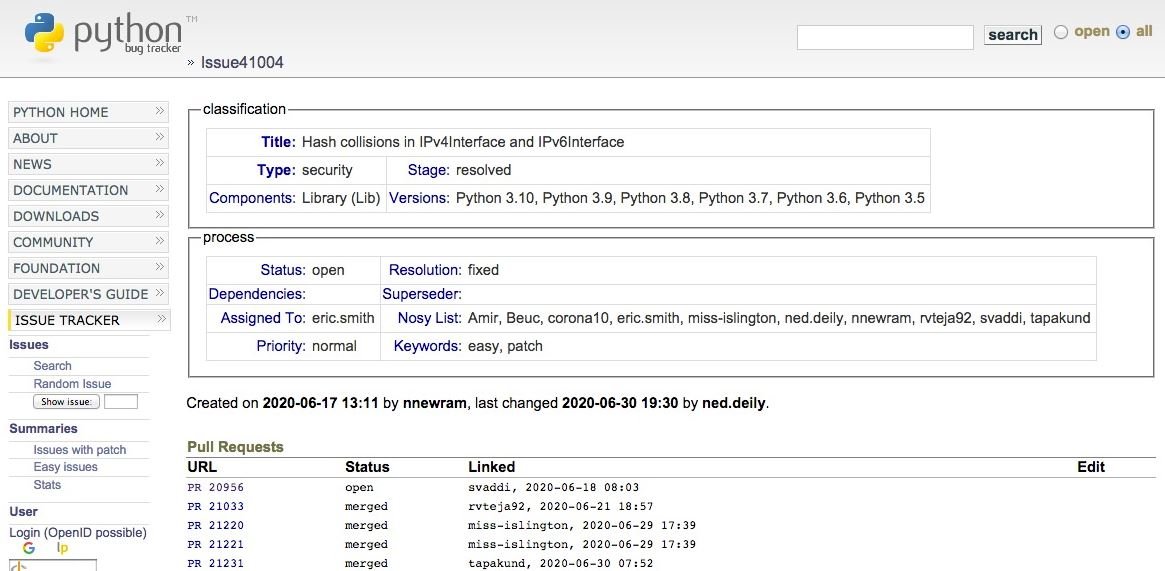
Tracked as CVE-2020-14422, this vulnerability exists because the application incorrectly calculates hash values in the IPv4Interface and IPv6Interface classes within Lib/ipaddress.py in Python, which would allow remote hackers to deploy DoS attacks.
Threat actors can trigger the resource algorithm to perform the DoS attack if an application is affected by the performance of a dictionary that contains IPv4Interface or IPv6Interface objects, generating multiple dictionary entries, the experts of a pentest company.
The vulnerability received a score of 6.3/10 on the CVSS scale, so it is considered a medium security flaw. The flaw resides in the following Python versions: 3.8.0, 3.8.1, 3.8.2, and 3.8.3.
Although the vulnerability can be exploited by unauthenticated remote hackers over the network, experts from a pentest company have not yet detected cases of active exploitation. Researchers have also not detected the finding of any malware variant linked to this attack. The bad news is that there is no patch to fully mitigate the risk of exploitation.
For further reports on vulnerabilities, exploits, malware variants and computer security risks, it is recommended to enter the website of the International Institute of Cyber Security (IICS), as well as the official platforms of technology companies.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











