Cybersecurity firm FireEye has launched a new open source tool called CAPA, which provides users with a framework dedicated to analyzing potentially malicious programs, as mentioned by malware reverse engineering specialists.
By using CAPA, researchers will be able to encode, recognize, and share information about the behavior of multiple malware variants, forming one of the largest databases of reverse engineering information, which will help predict the functions of previously unidentified malware variants. Below we will discuss some of the most important aspects of CAPA, which is now available to interested users.
Even though any forensics investigator can quickly understand how a file works in general, there are elements that escape even out of the experts’ view. Knowing if a program is malicious, understanding how it works during an attack, or determining developers’ intentions require greater malware reverse engineering skills.
While less specialized analysts have problems at this point in an investigation, a malware expert will be able to perform unknown binary classifications in no time, making it easier to get clues about the malware variant analyzed, a critical element in guiding successful research. Unfortunately, traditional analysis tools (string viewers/FLOSS) have several limitations, forcing users to obtain information by other methods.
It is necessary to remember that malware analysis is a complex task, because sometimes the most important elements in an unidentified variant are hidden through a binary that could include thousands of functions, not to mention that malware reverse engineering evolves at all times, so the learning curve extends to unsuspected levels. Therefore, researchers need to accumulate knowledge across multiple levels and concepts, including information about the internal components of an operating system.
This should not mean those interested in malware analysis have to lose hopes and enthusiasm, as with sufficient study and practice it is possible to recognize the most important and less obvious capabilities in a malicious program, taking into account repetitive patterns of API calls, strings, among other elements. By using CAPA, experts can automate the collection of research-relevant information, reducing workloads significantly.
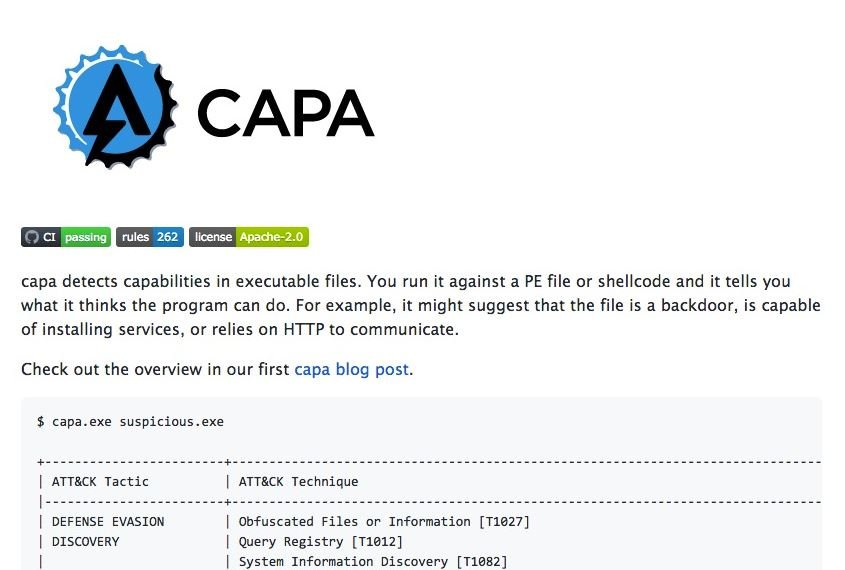
CAPA provides users with a unique, but able to adapt, method for coding knowledge about malware variants, in order to make it available to the cybersecurity community. When running CAPA, the tool will recognize some features and patterns just as the best malware analysts would, which is critical for further investigations.
An example of this can be seen when CAPA recognizes the unencrypted HTTP communication capability in the scanned software; for CAPA, this is a pass-through flag for proxy logs or other network traces.
CAPA developers believe that the cybersecurity community requires the creation of tools like this to significantly advance the most sophisticated malware variants in combat. Regardless of the level of research experience, CAPA contains more than a decade of knowledge and experience about the capabilities of the most dangerous programs created by hackers, facilitating combat to the most threatening cybercriminal practices. CAPA is available at the following link.
For further reports on vulnerabilities, exploits, malware variants and computer security risks, it is recommended to enter the website of the International Institute of Cyber Security (IICS), as well as the official platforms of technology companies.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











