Combating information technology threats depends on the collaboration of all members of the cybersecurity community, information security organization experts mentioned. The tech firm Corelight has decided to open source a tool for detecting exploitation attempts related to a critical vulnerability in Big-IP model load balancers, developed by F5 Networks.
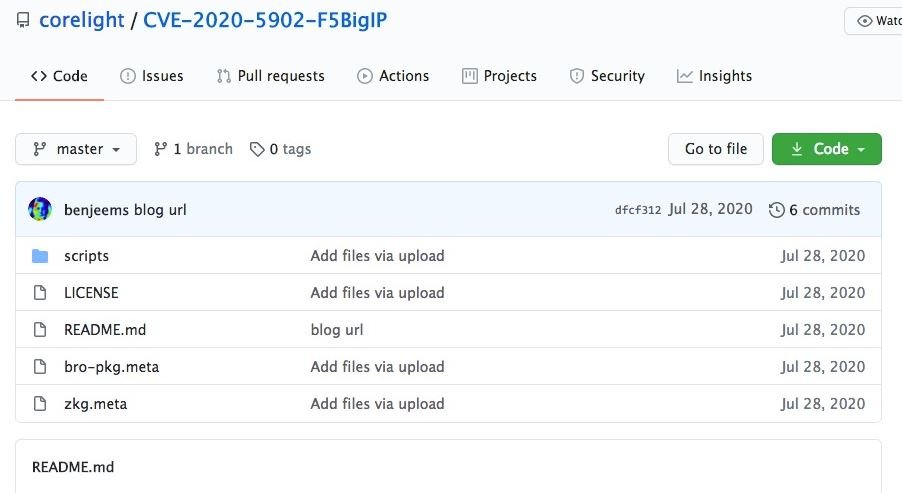
The open-sourced tool is Zeek, a network security monitoring software, which is now available in a GitHub repository. Zeek was designed by Lawrence Berkeley National Laboratory and is considered one of the most efficient network security solutions today.
According to information security organization experts, Zeek can be used in conjunction with Security Information Event Management (SIEM) systems, so that a network context is obtained to enrich sources of information.
In this regard, Corelight researcher Ben Reardon stated: “As responsible for incident response, it is always desirable to have contextual information in advance, because it is necessary to classify multiple factors quickly and clearly, so this is an excellent decision”.
“By adding elements as headers in the alert notice, Zeek gives researchers a clear advantage, as it won’t be necessary to go through data capture packets (PCAPs), speeding up decision-making about the next step in investigating malicious activity,” he added.
The cybersecurity community has begun alerting F5 users to the need to upgrade their devices, however, even updated deployment managers might be interested in detecting CVE-2020-5902 exploit attempts, a big-IP vulnerability that received a CVSS score of 10/10, information security organization experts mentioned.
This flaw resides in the Traffic Management User Interface (TMUC) configuration utility, and could be exploited with a simple line of publicly available code. Multiple firms and security researchers detected campaigns to exploit this flaw for a couple of months, allowing threat actors to install cryptocurrency mining malware, shell command execution, among other attack variants.
For further reports on vulnerabilities, exploits, malware variants and computer security risks, it is recommended to enter the website of the International Institute of Cyber Security (IICS), as well as the official platforms of technology companies.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











