Despite the risks many people continue to use sites on dark web sites for all sorts of malicious purposes, which can bring disastrous consequences. Recently Kristy Lynn Felkins, a woman from Fallon, Nevada, was arrested for allegedly trying to hire a hitman on an illegal forum to murder her ex-husband in 2016.
Currently there are multiple platforms on the dark web that offer services of hitters and even hitmen but, although many users ignore it, virtually all onion sites that offer contract killers are scams controlled by a single individual, usually identified as Yura.
Felkins was obviously unaware of this, so she somewhat carelessly began to forge a plan to murder her husband, as evidenced by court documents. Apparently, an informant monitoring these malicious sites provided authorities with a copy of the messages between Felkins and the alleged sicario.
Thanks to the informant, the researchers identified a user nicknamed “KBGMKN”, who appeared to be looking for a hitman on Besa Mafia, one of the dark websites linked to Yura, which are easily hackable. User KBGMKN registered on one of these sites using the email address ejggb133@sigiant.com; soon after, the researchers discovered that this username was composed of the initials of the names of Felkins’ children, so they linked this activity to the defendant.

In the conversations obtained by the authorities, Felkins is initially concerned about the legitimacy of the services offered on the website: “I found some posts on Reddit where it ensures that these sites are scams… Besides, how do you know if you’re with the FBl or not?” the defendant questioned the site administrator on the dark web.
Yura had already thought of an answer to these doubts: “These publications are made by undercover policemen; we don’t have time to deal with these signs but if you still decide not to negotiate online, you can look for a sicario on the streets.”
After being convinced, Felkins sent Yura nearly $5,000 through a Bitcoin transfer, along with multiple details that would help the alleged killer concrete the crime, including the victim’s home, a description of his car and some facts about his daily life. The defendant and the con man exchanged messages related to her plan for nearly a month until Yura finally mentioned that the work was about to take place in March 2016: “Everything is ready. The work will be done on Monday morning; let us know if the target will be accompanied by someone else. Our man will wait for him at work and shoot him as soon as the target gets out of the car,” the alleged hitman said.
However, the blow never happened, so the woman began to get impatient and press Yura to hasten her commission. A few days later, Yura asked him for $4,000 more because the job required a sniper; the fraudster found the perfect excuse to postpone the work when Felkins mentioned that her ex-husband would be traveling in some U.S. states. Faced with this situation, Yura offered to assassinate the individual at some point in his journey.
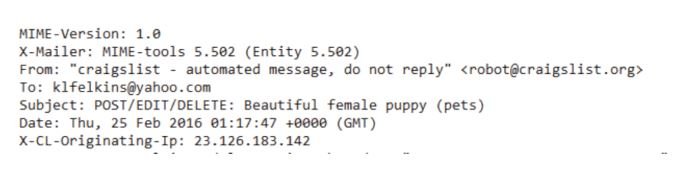
By this time of Felkins’ plan, the authorities had already detected the negotiation on the dark web forum, and found that the LocalBitcoins account used to pay Yura was linked to the defendant. The name that appeared on the LocalBitcoins account was “Kristy L Felkins”, who signed up with a Yahoo email address. Investigators obtained a court order to access the contents of this account, finding that the IP address was linked to the LocalBitcoins account from which the money was transferred to Yura.
With the evidence collected until then it was more than enough to arrest Felkins, who now faces charges that could lead to up to 10 years in prison. On his motivations, a snippet of the conversations between the defendant and the alleged hitman includes mentions of mistreatment against Felkins and his children, although the authorities continue to investigate the environment in which this family lived.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











