The U.S. Federal Trade Commission (FTC) filed a lawsuit claiming that the video conferencing platform Zoom has been lying to its users about the security of its end-to-end encryption at least since 2016. Although Zoom has already reached an agreement on these allegations, it has transcended in the media that the platform will not make any compensation to users affected by these non recommended practices.
In its internal documentation and propaganda, Zoom claims to have end-to-end encryption with 256-bit level. However, the constant scrutiny of the security of this platform showed that these claims were false, as Zoom provides a much lower level of security, potentially compromising millions of users.
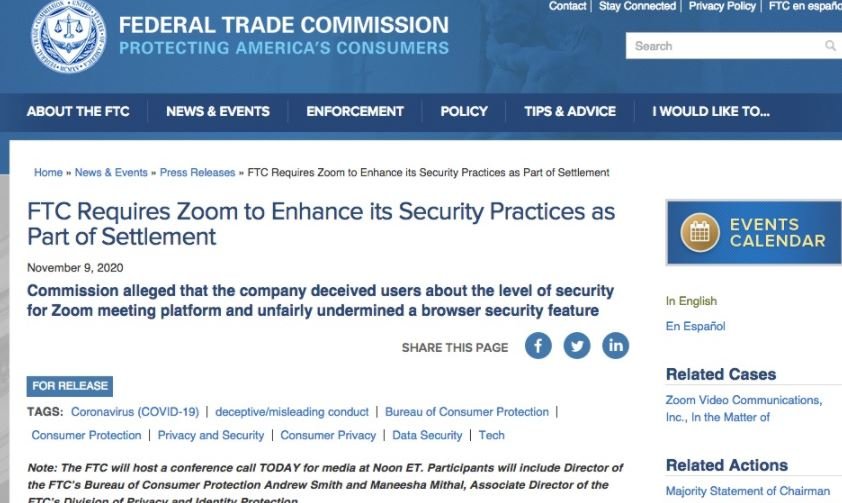
The FTC argues that the level of encryption Zoom uses is much lower than promised, so the company is committed to upgrading its systems and improving its user protection mechanisms. It is important to remember that the number of users of the company increased to almost 300 million people during the most recent months due to the pandemic.
“Zoom’s claims are misleading and harm users who have turned to this platform at a time as complex as the current one,” adds demand from the FTC. As part of the agreement between developers and authorities, Zoom will need to establish a system that actually complies with what its advertising documents mention. In other words, the platform will implement 256-bit end-to-end encryption as soon as possible.
As long as the implementation of this new encryption is realized, the company will respond directly to concern users any questions about the security of the platform.
Mac users were recently found to face a similar encryption issue related to “ZoomOpener”, which was installed secretly to avoid Safari security measures that open a dialog box before starting the application. The FTC is still deliberating on the case and Zoom is currently required to provide its 256-bit end-to-end security guarantee for its users.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











