This Is Why “Auto-Update” Is a Hacker’s Favorite Feature
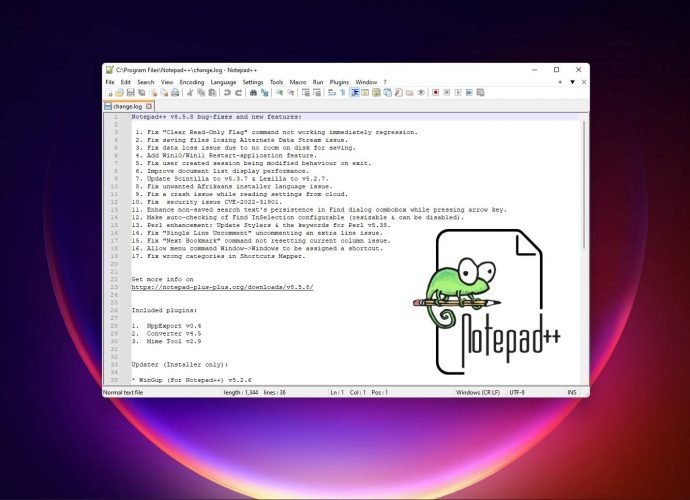
Between June and December 2025, the software update infrastructure supporting Notepad++ was covertly compromised and abused as a delivery mechanism for state-aligned cyber-espionage malware. The operation did not involve sourceRead More →