A group of specialists has detailed a method of cyberattack that could present severe risks for sectors such as biological research. This week, academics at Ben-Gurion Del Negev University described how uninformed biologists and scientists in cybersecurity could become victims of cyberattacks designed to take biological warfare to unusual levels.
This is especially dangerous at the present time, as a considerable part of the global scientific community is on the way to taking important steps in the search for possible coronavirus vaccines. According to the report, scientists could be tricked into producing highly dangerous toxins or viruses using malicious hacking campaigns.
This entire attack depends on the use of a malware variant capable of infiltrating the computer equipment of one of these researchers. Once inside, threat actors could replace substrings in the DNA sequence using simple obfuscation processes and deceiving users of a widely used system in the field of medical research.
“The U.S. Department of Health and Human Services (HHS) requires potentially harmful DNA detection protocols to be established, however, by using this attack, hackers could circumvent security mechanisms to disrupt advances in these investigations and turn projects aimed at saving millions of lives into deadly biological weapons,” the report states.
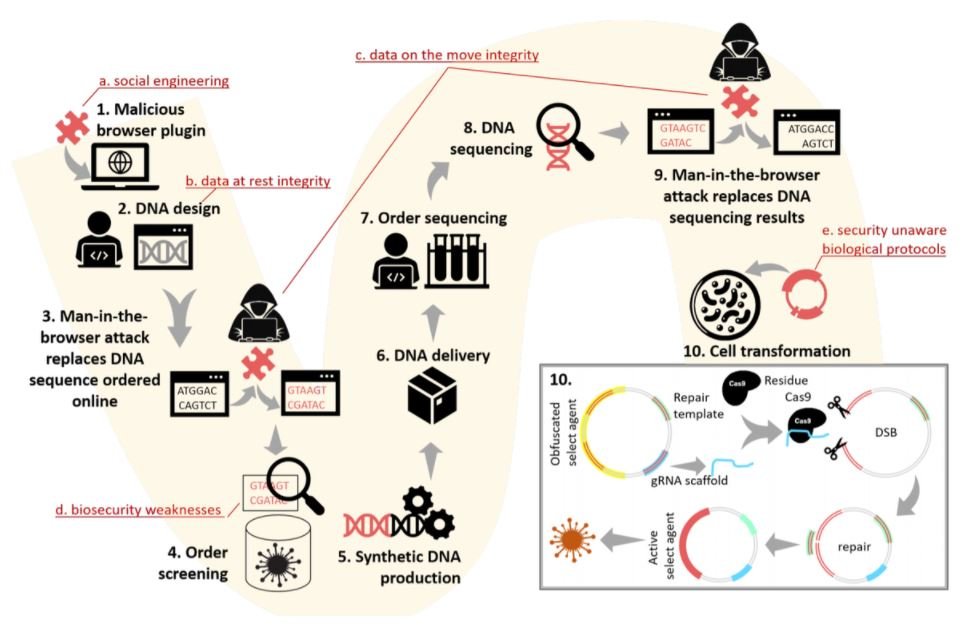
Software used to design and manage synthetic DNA projects may also be susceptible to Man-in-The-Middle (MiTM) attacks, allowing hackers to inject arbitrary DNA chains. “Remote hackers could use malicious extensions or any other attack variant based on a web browser,” the experts add.
Rami Puzis, one of the specialists who collaborated in this investigation, believes that the risks identified in this process should not be dismissed: “This attack scenario underscores the need to strengthen the synthetic DNA supply chain with protections against a combination of biological and cyber threats. To address these threats, we propose an improved detection algorithm that takes into account in vivo gene editing,” adds the expert. The investigation is still ongoing, so more details could be revealed shortly.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











