Security researchers from an Austrian company have disclosed dome details about a severe vulnerability in Microsoft Autopilot, the tool for deploying devices in corporate networks. According to the report, successful exploitation of this flaw allows threat actors to take control of a complete IT system. The company’s spokespersons have denied this issue.
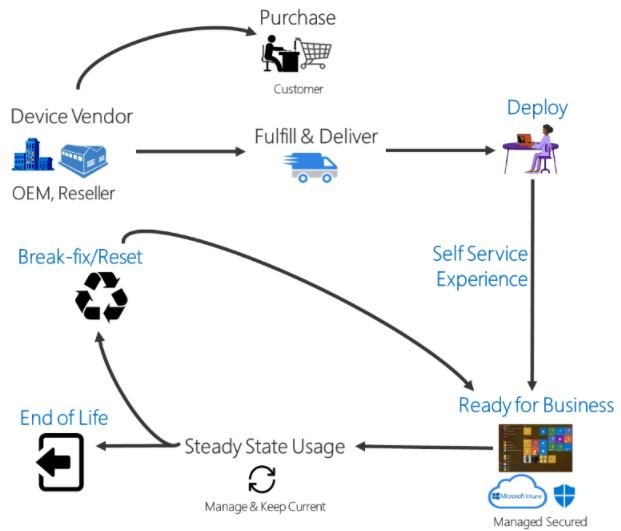
Windows Autopilot allows to easily pre configure and set up new devices without a dedicated infrastructure on the client’s premises. In the Microsoft Endpoint Manager Admin Center, the IT department defines a Windows Autopilot deployment profile that can be assigned to all devices or pre-defined groups. When initially deploying new Windows devices, Windows Autopilot uses the OEM-optimized version of Windows 10.
The security problem affects the Autopilot deployment process and allows an attacker or low-privileged user to perform a privilege escalation attack to the local administrator level. This is possible even if the following rules are specified in the Autopilot profile: new users are added to the regular unprivileged users group, adding new local administrators is prohibited, and running CMD via Shift + F10 in the OOBE interface is also prohibited.
Any malicious hacker willing to exploit this flaw first has to enable the device (previously added to Intune by manually downloading a unique hardware hash). According to the report, the vulnerability is then manually thrown by physically removing the TPM security device; that is, disconnecting it from the virtual machine in use. In this case, the deployment will suddenly shut down.
When admins open a window with an error message, they need to click on the ViewDiagnostics option, and then select the Rundll32.exe\\10.0.0.1\shell.dll, DLLMain folder. This way, a shell connection is established with the attacker’s host as the default user – defaultuser0. This user gets administrator privileges.
To bypass the UAC system, researchers used StoreFileSys, having the ability to create a local user with administrator rights or implement other backdoors. The device connects back to the local network, the software installation resumes and runs successfully, so that the user defaultuser0 is removed, but the local elevated users created by it are preserved.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











