A recent report by security firm Citizen Lab states that dozens of journalists were victims of an espionage campaign in which their mobile devices were compromised with a malware variant used by nation states. Affected journalists work for al Jazeera news agency, and would have been attacked through a zero-click attack based on a critical vulnerability in iMessage, Apple device messaging app. Hackers managed to hack compromised smartphones without requiring victims’ interaction.
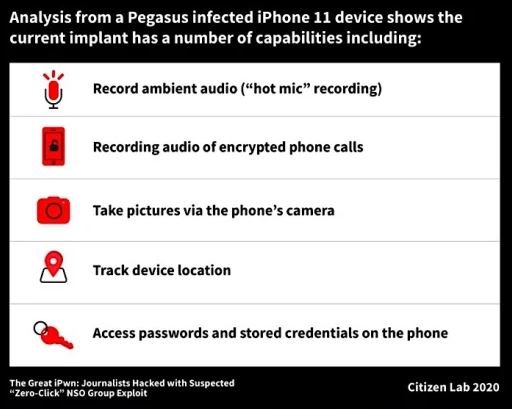
The report mentions that the compromised iPhones were infected with Pegasus, the spyware developed by the Israeli firm NSO Group. Investigators analyzed journalist Tamer Almisshal’s device and discovered that, between July and August, his iPhone connected to NSO Group’s servers without apparent explanation. Experts believe that threat actors would have activated the microphone of infected devices, as well as taking photos with the camera, accessing users’ passwords and tracking the location of victims.
Experts say most of the attacks would have been deployed by four of NSO Group’s clients, including countries such as Saudi Arabia or the United Arab Emirates. However, the clear interest in accessing the devices of Al Jazeera reporters indicates a specific campaign deployed by a country that has not been named.
NSO Group is known for its relationships with multiple national states, to which it provides the tools needed to deploy complex espionage campaigns against political opponents, activists, journalists and even entrepreneurs. Previous reports indicate that countries such as Saudi Arabia have used NSO solutions to spy on communications from prominent journalists who have been the victims of attacks and have even died, as is the case with Jamal Khashoggi.
Investigators concluded their report by pointing to an “accelerated espionage trend” against journalists and news agencies. To do this, attackers exploit little-known vulnerabilities in communications systems, achieving important results without victims being able to detect signs of malicious activity.
After receiving constant requests for information, NSO Group issued a statement dismissing these signals, although this is the measure that the company implements each time it is informed of this conduct.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











