Alphabet Inc., through its cybersecurity subsidiary Jigsaw, announced the launch of Outline, a project that allows any user to create and run their own virtual private network (VPN) server to provide other users with these features.
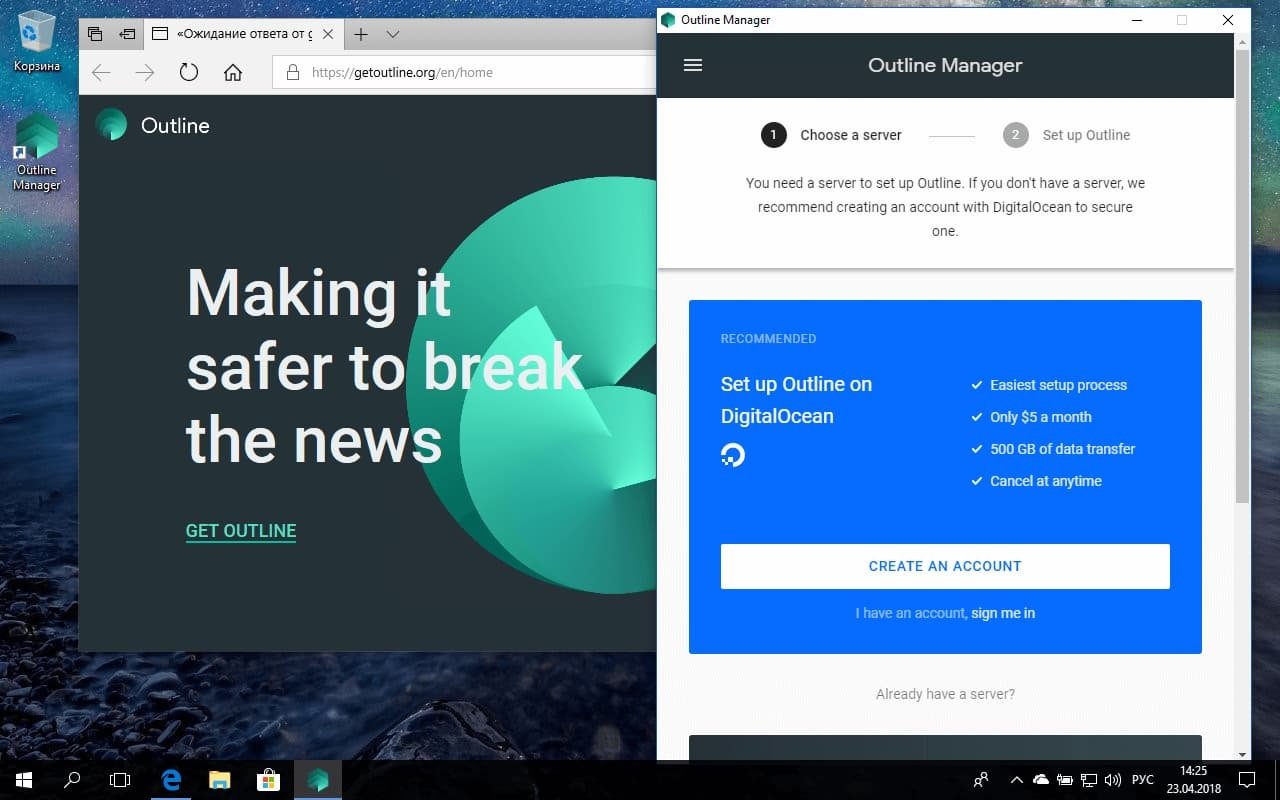
According to the experts in ethical hacking of the International Institute of Cyber Security (IICS), there are two main components in Outline: the Outline Manager control application, and the client. Outline Manager is based on the Electron framework and is available for Windows, Linux, and macOS systems.
You can create a VPN server in another hosting service. Outline’s goal is to make it as easy as possible to launch your own VPN service. If you choose DigitalOcean, for example, a web page will open in the application where you will need to enter your username, password and one-time code. You must then enable Outline to use the DigitalOcean API, thus completing the preset process.
The next step is to create a VPN server, mentioned by ethical hacking experts. By default, Outline chooses the cheapest DigitalOcean plan ($5 USD per month for 1 TB of traffic). DigitalOcean data centers are located in 8 different cities around the world: Amsterdam, Singapore, Bangalore, Frankfurt, London, San Francisco, Toronto and New York.
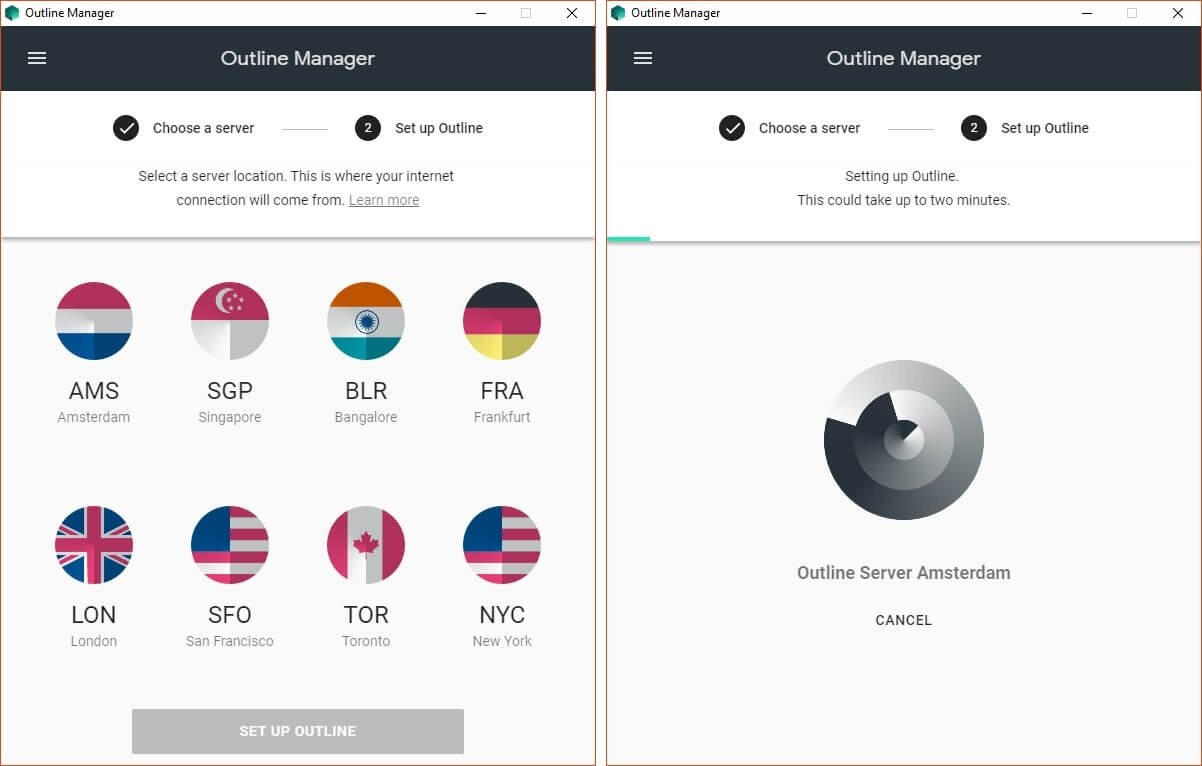
Next, you’ll need to choose a city, so that the management application automatically downloads the image from the Docker container and creates a server in DigitalOcean based on this image. The software on this server will be automatically updated every hour, mentioned by ethical hacking experts.
DigitalOcean will automatically perform security updates for the operating system and restart when necessary, mentioned by ethical hacking experts; you can control your own VPN server from the management application. By default, Outline generates only one key per user; however, you can add new users to the server to invite friends or colleagues.
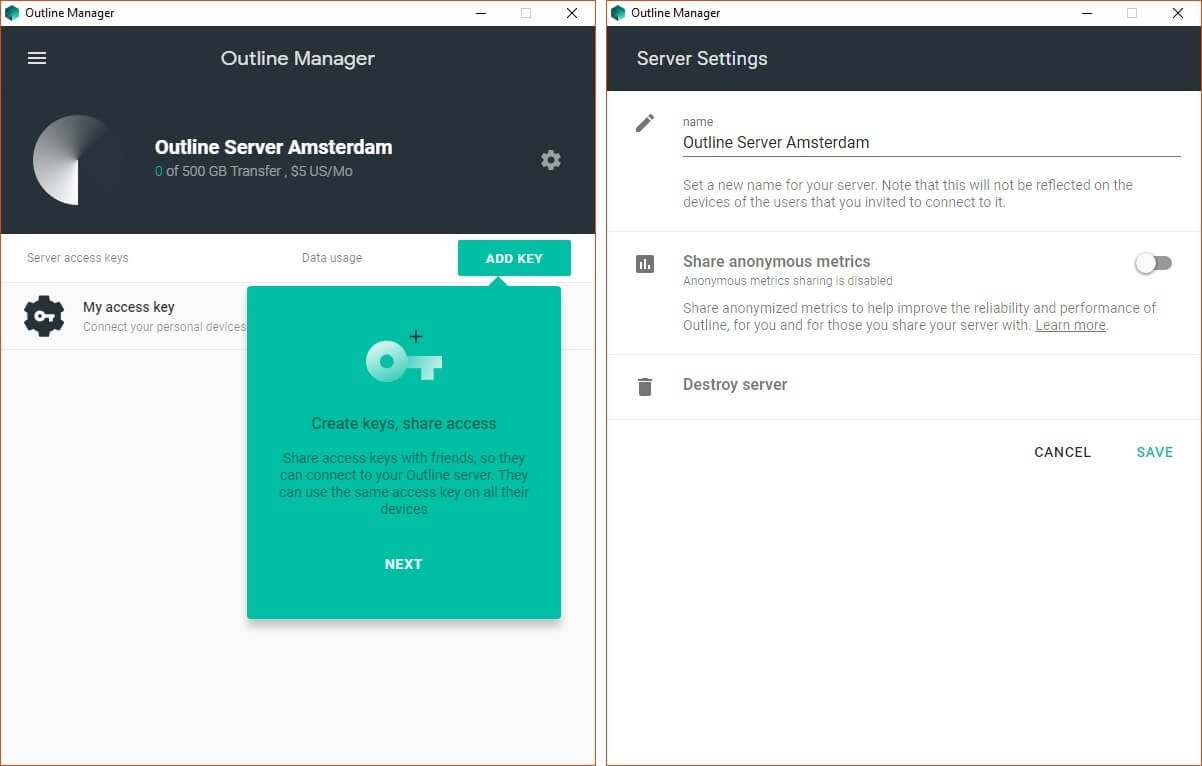
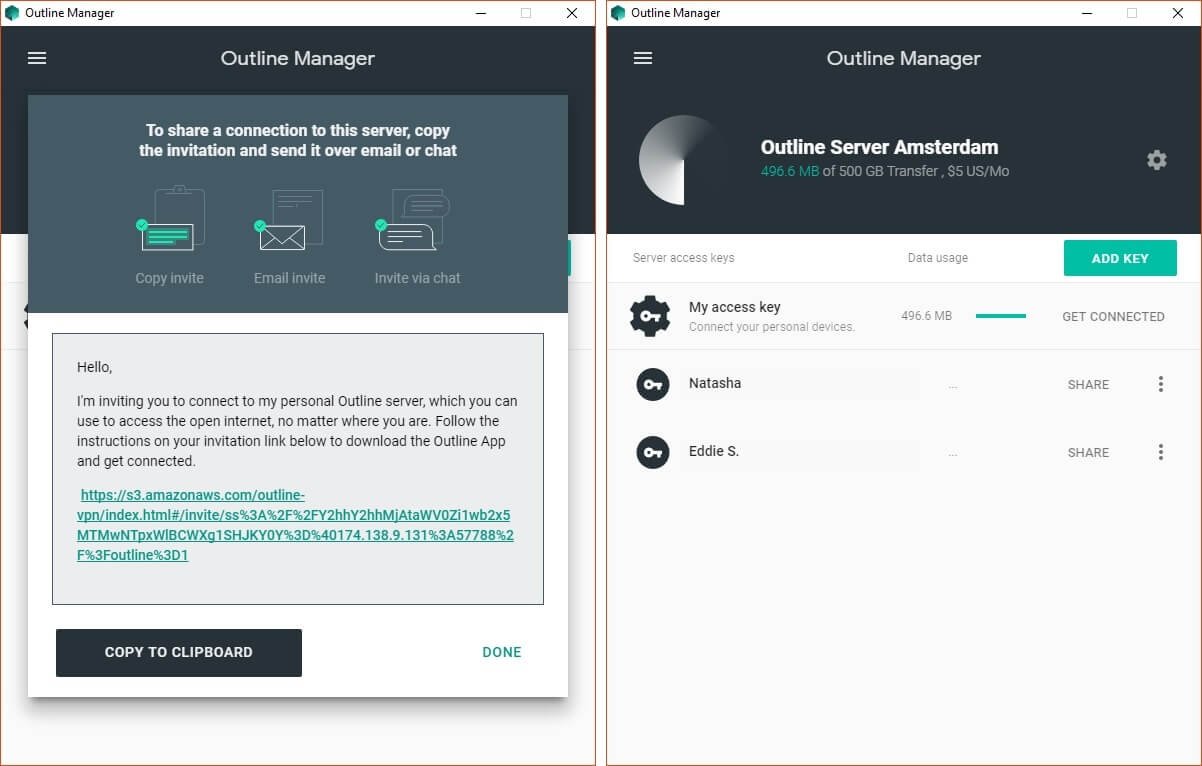
Outline Manager allows you to add or remove servers and restrict access to users; this application will also show us information about the traffic consumption of registered users. On the other hand, the invitation website is a static Amazon Web Services (AWS) platform with two main elements:
- The page invites users to download the client app to their devices
- Users receive a unique key that is part of a URL. The browser displays the given key when you load the page
It is worth noting that you should not invite other users through non-encrypted channels such as Facebook or via email.
Connecting to the VPN server is relatively simple. All that is required is to install the app or click on the invitation link.
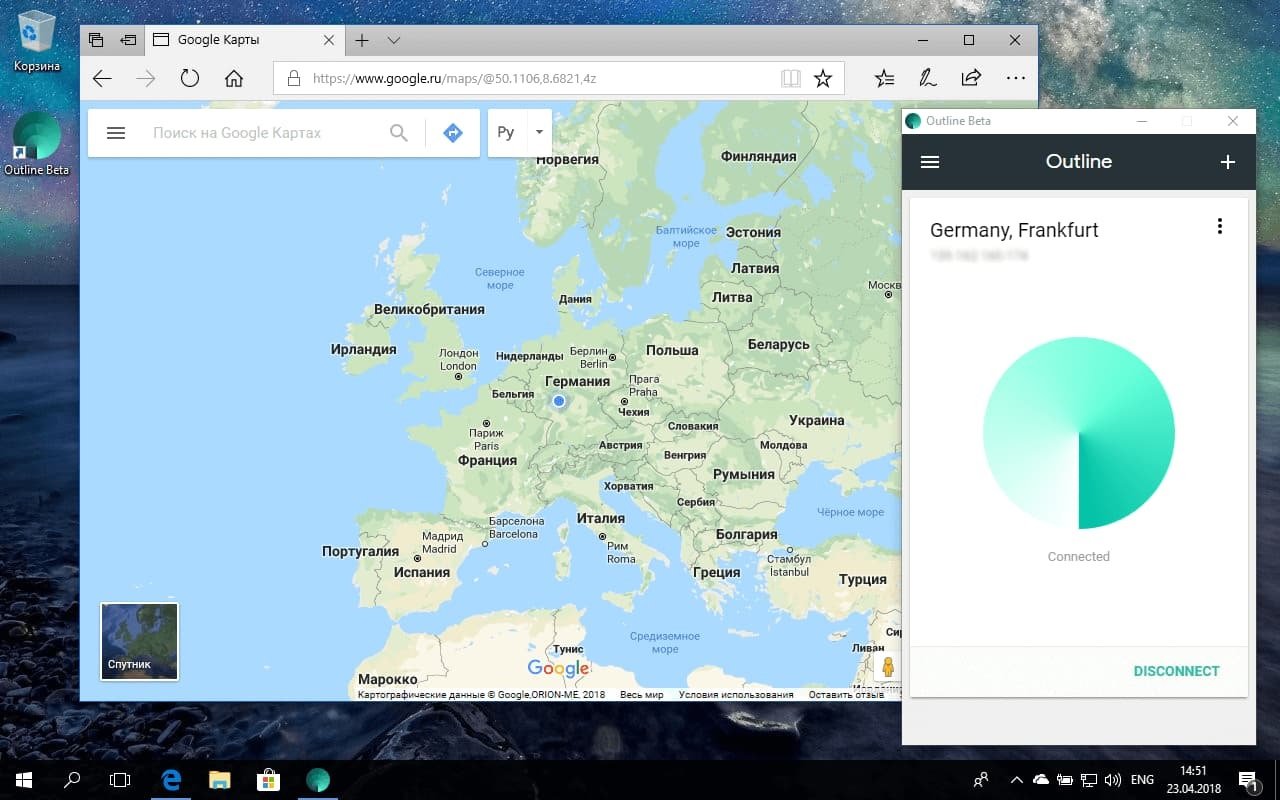
The client app for connecting to the VPN server is available for Windows, Android OS, macOS system, and iOS platforms. This consists of a very simple interface that only allows you to connect or disconnect from the server.
A good alternative to conventional VPN services
Ethical hacking experts point out that Outline uses the Shadowsocks protocol, very different from other options such as OpenVPN, IPSec, and WireGuard, mainly because it is not a VPN protocol.
Shadowsocks is an open source project to create a SOCKS5 encrypted proxy server to redirect Internet traffic. Technically, a VPN is an encrypted tunnel between a device and a server, so all this traffic passes through the tunnel, interacting with the public Internet. Using Shadowsocks, you can be absolutely sure that your Internet provider will not be able to interfere with your traffic, as well as access restricted sites only for some geographic areas.
However, this approach also has its disadvantages. As with other VPN options, anyone with access to the VPN server might see your network traffic, this information might end up in the hands of marketing companies or even other VPN service providers.
The SOCKS5 proxy looks like normal Internet traffic, so Shadowsocks combines the benefits of a proxy with traffic encryption. Still, users can’t be sure that all network traffic passes through the proxy server; because it all depends on the specific application. Outline can be a great tool if you want to access blocked sites in your browser, but this connection will not provide a complete anonymity of your online activity.
What role does Google play here?
While this is a fully funded project by Google and its parent company, Jigsaw’s involvement appears to be a clear message of support for the trust of external developers, who can collaborate directly with Outline as it is an open source project.
Jigsaw collects anonymous reports of service failures, as well as gathering information about the IP addresses of all servers, but without the ability to access them. If users wish, they can share additional information about their network traffic.
Conclusions
The main challenge for tool developers like Outline is affordability, although ethical hacking experts believe that more remarkable efforts must be made to refine this platform, although the first steps are certainly best suited to drive a project with great potential.
Outline could become a large-scale solution for users in countries like China, who face strict restrictions on their Internet access, not to mention that it could be consolidated as a more secure option than any other VPN service available today.

Information security specialist, currently working as risk infrastructure specialist & investigator.
15 years of experience in risk and control process, security audit support, business continuity design and support, workgroup management and information security standards.











