Luan Herrera, a cybersecurity specialist dedicated to vulnerability reporting, detailed a new way to perform a side channel attack variant known as XS-Leak abusing redirect hops to trigger a cross site leak condition.
Herrera’s research, available on Google Docs under the title “XS-Leaks Failures in Redirect Flows”, focuses on the XS-Leaks family of side channel attacks, capable of abusing a browser to extract potentially sensitive information into the exposed system, including administrator credentials.
XS-Leak attack methods rely on measuring network response time to collect data about website visitors by abusing communication channels that allow websites to communicate with each other to reconstruct a user’s or system’s profile.
The documents mention a “novel technique” for abusing a limitation in the Fetch specification, a way that allows websites to call resources: “A limit of 20 redirect hops is set before a network error message appears; because of this limit, threat actors could count the number of redirect hops that occur in a cross-origin redirect by activating the redirect before reaching the victim’s endpoint, measuring network responses, and partially exposing the size of the URL list,” the report says.
The expert also detailed some ways to detect and prevent these cross-redirects that can lead to a side channel attack, including the use of SameSite cookies, COOP and frame protections. Google is also aware of this problem, so measures such as isolating some chrome-accessible websites have already been announced to reduce the amount of information exposed in a possible side channel attack.
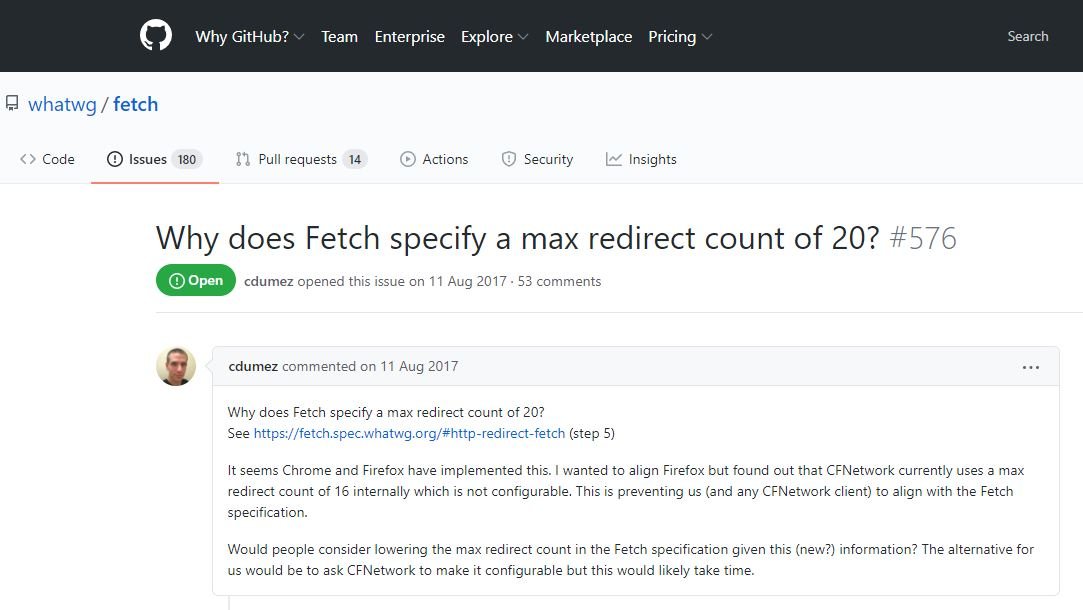
Herrera agrees that this attack can be prevented in the same way that similar attack variants are prevented, although he believes that a holistic view of the problem is required: “A comprehensive view of the problem is still being discussed on GitHub about whether it is possible to change the Fetch specification and the limit value in order to prevent the appearance of these attack variants,” adds the researcher.
The report also includes the results of a challenge to deploy an XSS attack using JavaScript code. A Google security expert known as “terjanq” also conducted an investigation into the XS-Leak family of attacks, describing the launch of a cache polling attack against a small group of Google products, which could deploy a leak of sensitive information.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











