Google Project Zero researchers revealed the finding of a critical vulnerability present in Windows systems that could be exploited to deploy remote code execution attacks. Tracked as CVE-2021-24093, the vulnerability was fixed in the latest update package released by Microsoft. Project Zero is a team of security researchers formed by Google in charge of analyzing potential security risks and discovering zero-day vulnerabilities.
Remote code execution refers to a threat actor’s ability to execute arbitrary commands or inject remote code into a remote target system in order to deploy subsequent hacking tasks.
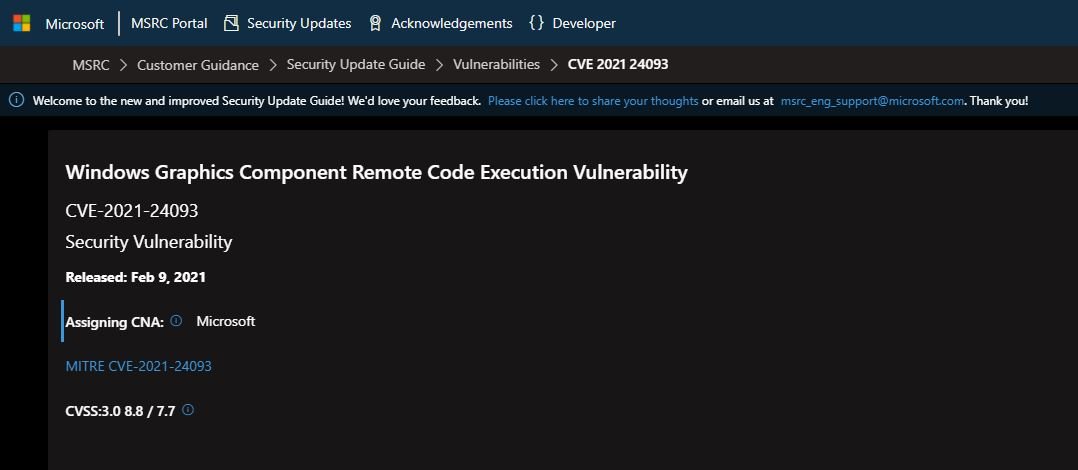
The flaw received an 8.8/10 score according to the Common Vulnerability Scoring System (CVSS), in addition to receiving a “critical” rating from Microsoft. Affected operating systems include Windows 10, Windows Server 2016, and Windows Server 2019. The company mentions that this security flaw resides in a graphical component of Windows and can be exploited via malicious websites.
Google Project Zero researchers reported this security flaw to Microsoft in late November 2020. The report was released last Wednesday, just two weeks after the company released the patches needed to mitigate the risk of exploitation.
Experts mention that CVE-2021-24093 is a buffer overflow flaw based on the DirectWrite heap and is directly related to processing a specially designed TrueType font. According to the report, a threat actor might trigger a memory corruption condition to execute arbitrary code in the context of the DirectWrite client.
It should be noted that DirectWrite is a Windows API specially designed to render you text in high quality.
Experts developed a proof-of-concept exploit, successfully committing vulnerable systems at a testing stage. However, because some pre-attack conditions are required, Microsoft rules out the possibility that the flaw may be exploited in the wild.
To learn more about information security risks, malware, vulnerabilities and information technologies, feel free to access the International Institute of Cyber Security (IICS) website.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











