SAP security teams announced the release of nine security updates to fix some flaws, two of which were considered critical. The most dangerous vulnerability, tracked as CVE-2021-21480, received a score of 9.9/10 according to the Common Vulnerability Scoring System (CVSS) scale.
Successful exploitation of these vulnerabilities would allow threat actors to intercept requests to the server, inject malicious JSP code and forward it to the server, deploying a kind of Man-in-The-Middle (MiTM) attack.
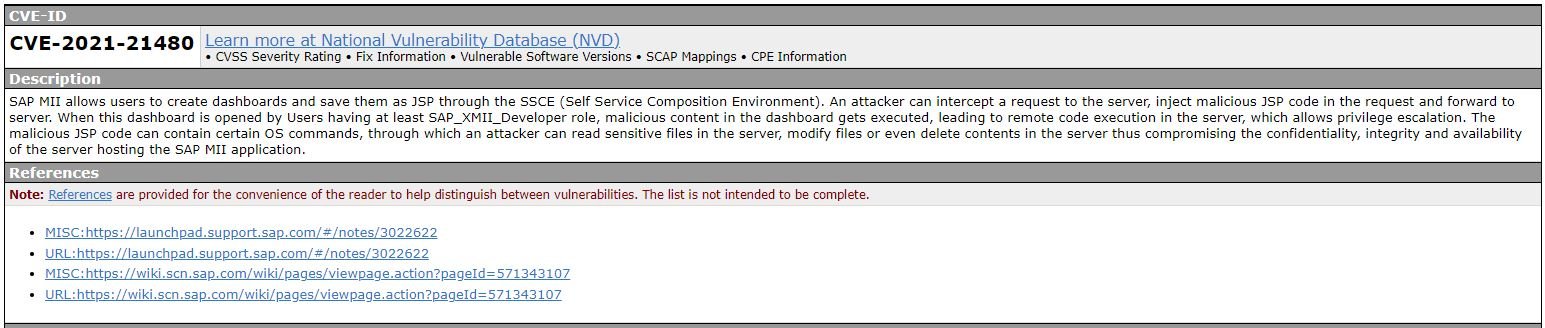
A National Vulnerability Database (NVD) report adds more details about this security risk: “When SAP_XMII_Developer role users open this pane, malicious code runs, which will eventually trigger an escalation of privileges. This malicious JSP code may contain operating system commands through which a user can read sensitive files on the server, modify files, and even delete content from the target server.”
Another reported flaw, tracked as CVE-2021-21481, was described as a missing authorization check in SAP NetWeaver and received a score of 9.6/10. This flaw presents threat actors with the opportunity to take full control of the target system: “MigrationService, present in SAP NetWeaver versions 7.10, 7.11, 7.20, 7.30, 7.31, 7.40, 7.50, fails to perform an authorization check, allowing hackers to access configuration objects with administrative permission.”
On the other hand, among the remaining flaws stands out the one tracked as CVE-2021-21484, an authentication bypass in the SAP HANA v2.0 database. The rest of the bugs fixed in this update are minor bugs in SAP’s various enterprise products, in addition to other lower severity flaws reported a few months ago and without evidence of active exploitation cases.
In a separate report, Microsoft announced the release of various updates for Exchange Server after receiving reports on multiple security incidents. The company even released some updates for its Internet Explorer browser, even though it has already been replaced by Microsoft Edge and very few individuals and organizations continue to use this tool.
In this regard, software engineer Adam Bunn mentions: “Since it was discontinued in November 2020 we have stopped seeing updates for Internet Explorer; Microsoft detected active exploit cases related to CVE-2021-27085 and CVE-2021-56411, so we recommend that you install these security patches if you are still using Internet Explorer.” To learn more about information security risks, malware variants, vulnerabilities and information technologies, feel free to access the International Institute OF Cyber Security (IICS) website.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











