In its most recent security alert, the Federal Bureau of Investigation (FBI) unveiled the detection of a wave of Conti ransomware attacks targeting first aid and health care networks in multiple U.S. government organizations, including implementations in utility offices and law enforcement agencies.
The ransom note sent by the hackers requires administrators of the affected systems to contact them through their platform on dark web to begin negotiations. It is further specified that, in case of not paying the ransom, the compromised data will be deleted or sold on illegal hacking platforms. The amount of a ransom may vary, although Conti hackers have come to demand up to $25 million USD as a ransom.
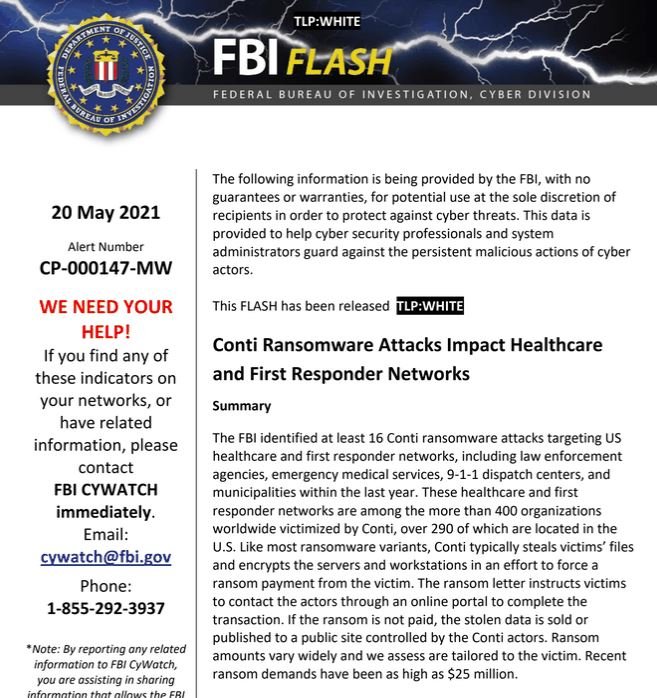
The federal agency ensures that these attacks target networks employed by emergency services personnel, which can delay the process of responding to medical incidents. Loss of access to these systems can be catastrophic for affected organizations.
Hackers gain unauthorized access to affected organizations’ networks through phishing campaigns, Remote Desktop Protocol (RDP) credential theft, and other attack variants. Malicious documents created by Conti hackers are infected with agents like Cobalt Strike, allowing them to first access the affected network.
Hackers can spend between a week and twenty days idle on affected networks before starting the attack, using DLL libraries for payload delivery. Threat actors first use tools that are already available on the network and then add other utilities as the case may be, including Windows Sysinternals1, allowing them to scale privileges, move over the affected network, and eventually complete the infection.
Once Conti actors install the ransomware on the affected system, they can gain persistence on the network and issue a beacon using Anchor DNS. Victims have two to eight days after the infection is completed to respond to the ransom demand. If the deadline expires and a payment has not been completed, hackers begin making calls to administrators of affected systems using Voice over Internet Protocol (VoIP) technology, following threats until the demanded ransom is obtained.
In addition to a detailed description of these attacks, the FBI also issued a number of recommendations to act before and after a ransomware attack, including measures such as proper maintenance of backup systems, use of virtual private networks (VPNs), and use of strong passwords, among other measures.
To learn more about information security risks, malware variants, vulnerabilities and information technologies, feel free to access the International Institute of Cyber Security (IICS) websites.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











