Cybersecurity specialists reported the detection of an ambitious phishing campaign in which operators try to trick users while posing as employees of a paid service that must be cancelled. The goal of these hackers is to infect the attacked systems with the BazaLoader malware variant.
This malware is able to implant a backdoor on Windows systems, allowing the deployment of subsequent attacks such as Ryuk ransomware infections, which is usually delivered via BazaLoader. The latest campaign depends on the interaction of affected users, plus a complex chain of attack is required to complete a successful infection.
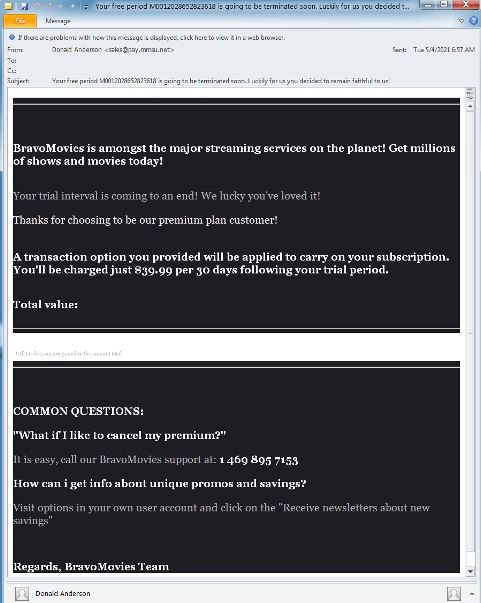
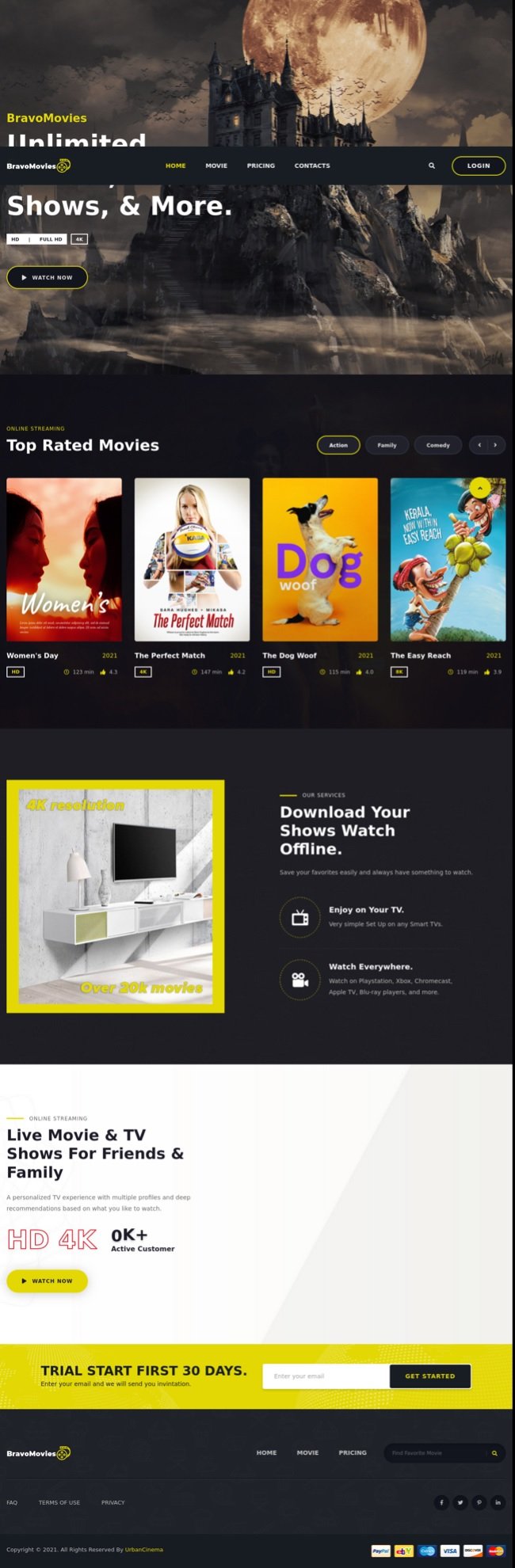
Researchers at security firm Proofpoint mention that the first stage of attack begins with the deployment of thousands of malicious emails allegedly sent from a fake streaming service named “BravoMovies”, a name used by hackers to trick victims.
Hackers seem to have devoted many resources to creating the website, even remembering movie posters to make it more attractive. However, more analytical users will notice some spelling errors on this platform.
The message received by the affected users ensures that the victim’s trial period is over, so a charge of $40 per month will start unless the user decides to cancel by calling the phone number provided in the message. If the user decides to call, they will be contacted by a supposed customer service representative who, pretending to help cancel the service, will be forcing the installation of the malware on the victim’s computer.
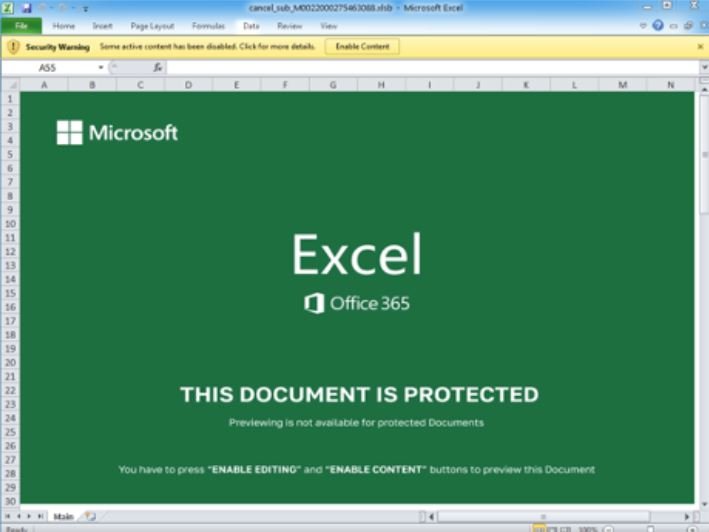
Hackers achieve the infection by directing the user to a fake subscription website, where the user will be attempted to download an Excel document. This document contains macros that, when enabled, will download the BazaLoader malware to the compromised device. This is another example of how social engineering can be very useful in deploying an attack on hundreds and even thousands of users, allowing hackers to work almost automatedly and make huge profits on reduced time windows.
For security reasons, users should ignore these kinds of messages, as it is clear that these are very well designed but flawed electronic fraud attempts that give away the intentions of hackers. This is an effective technique because hackers threaten to charge users’ cards, so it creates a sense of urgency on the affected user.
To learn more about information security risks, malware variants, vulnerabilities and information technologies, feel free to access the International Institute of Cyber Security (IICS) websites.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











