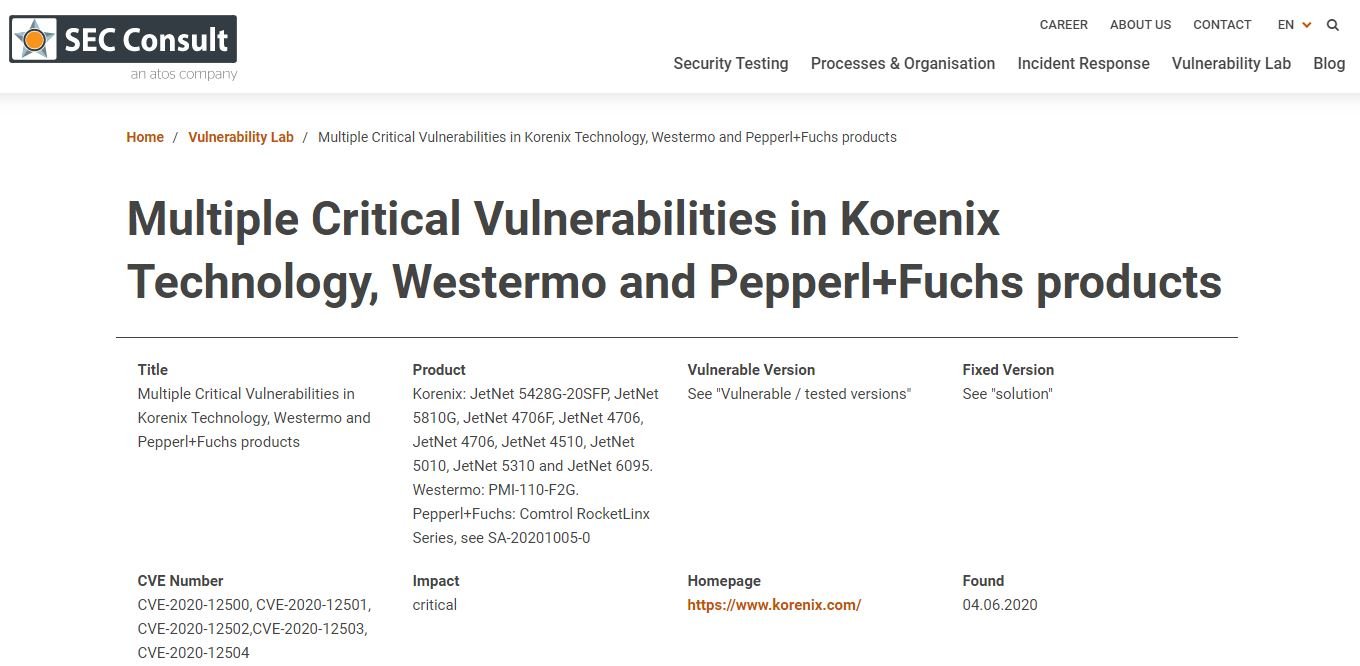
A recent security report states that industrial switches created by major technology manufacturers could be affected by a specific set of vulnerabilities because they share the same firmware, developed by Taiwanese company Korenix Technology. These flaws were identified by cybersecurity firm SEC Consult, whose researchers have been trying to address these bugs since early 2020, though the firmware developer took nearly a year to release the required security patches.
According to the report, all drivers from companies such as Westermo or Pepperl+Fuchs share the same firmware base, so they are affected by the same vulnerabilities. The researchers discovered five critical vulnerabilities that could affect these devices, including unauthenticated device management flaws, backdoor accounts, cross-site request forgery (CSRF), among other issues.
Threat actors with network access to a vulnerable device could make unauthorized changes to its configuration, lead to a denial of service (DoS) scenario, and extract sensitive information. The vulnerabilities would even allow attackers to take full control of the affected devices.
Vulnerable devices are used in multiple industrial sectors, including transportation, energy, automation, security systems and other industrial sectors. Thomas Weber, a researcher at SEC Consult, mentions that the affected switches are deployed in key sectors, so hackers could exploit these flaws to disrupt the network connection to the underlying systems.
The expert also mentioned that only a set of vulnerable devices are exposed on the internet, so the risk of exploitation is not too high. While some flaws can be abused to launch attacks remotely, Weber points out that the protections of these devices make exploitation difficult.
After receiving a security alert, Pepperl+Fuchs released some patches during 2020, although these flaws persist due to the main issue residing in Korenix firmware.
While the company delayed the release of the security patches, the updates are now ready to be installed on vulnerable devices. In addition to releasing firmware updates, Korenix shared some recommendations to prevent potential attacks, including restricting access to devices, implementing security best practices, and special firewall configuration.
To learn more about information security risks, malware variants, vulnerabilities and information technologies, feel free to access the International Institute of Cyber Security (IICS) websites.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











