A recent cybersecurity report mentions that a group of threat actors may have abused a security flaw in the chat service built into Microsoft Teams that would have allowed them to impersonate an employee of an affected company in order to send emails for malicious purposes. Evan Grant, the expert in charge of the report, mentions that the flaw lies in Microsoft Power Apps, a platform for developing low-code or no-code applications.
Although the attack requires multiple elements to materialize, the final exploitation is simple and its impact can be highly detrimental to users: “The flaw can be exploited to establish persistent read/write access to the affected user’s Microsoft infrastructure, including Teams chat, OneDrive and SharePoint,” the expert points out.
The attack can be carried out using a malicious Teams tab and abusing Power Automate flows. Grant presented his finding to Microsoft security teams and the flaw was corrected a short time later.
In his report, the expert described a hypothetical scenario in which an attacker (identified in the experiment as baduser@fakecorp.ca) could create a malicious Teams tab and use it to steal emails, messages, and files from Teams on behalf of a legitimate user. Unrestricted access to users’ inboxes represents a great opportunity for threat actors, actually constituting an enterprise email engagement (BEC) scenario.
As some users may remember, in a BEC attack the threat actors pose as members of the affected company to try to trick legitimate employees in order to divert money to accounts controlled by hackers. These attacks require hackers to collect a large amount of information about the companies targeted, including organizational chart, job names, work routines, financial statements, and security practices.
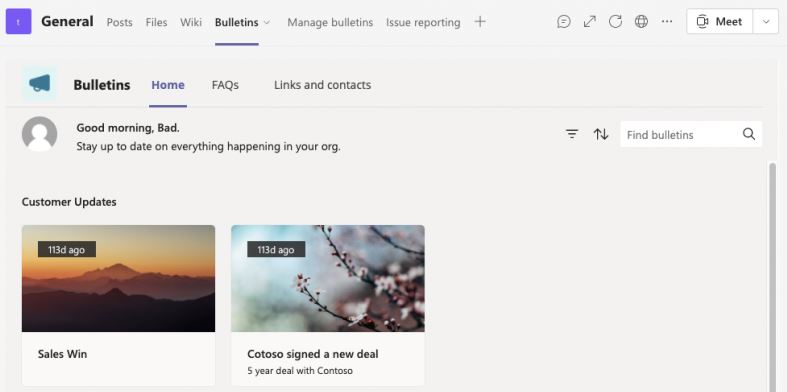
This attack starts with the creation of the malicious Teams tab. Grant performed this procedure by abusing a feature on the platform that allows users to launch small applications in any workgroup of which they are members.
Once this malicious tab is created, threat actors can pose as legitimate users and steal authentication tokens, in addition to deploying attacks typical of a BEC scenario. Microsoft has already updated the affected deployment, so the risk is expected to have been fully mitigated.
To learn more about information security risks, malware variants, vulnerabilities and information technologies, feel free to access the International Institute of Cyber Security (IICS) websites.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











