GitLab’s security teams announced the fix of a server-side request forgery (SSRF) flaw recently reported by an independent researcher. As some users will recall, an SSRF attack occurs when a threat actor forces a vulnerable server to connect to internal services within the infrastructure of the maliciously targeted organization.
In December 2020 the researcher known as “Vin01” discovered that GitLab Lint CI API was affected by multiple flaws, which were reported to the appropriate security teams. Finally, GitLab released a security patch in early 2021, allowing the researcher to publish a full report on the bug.
The affected API is used to validate the YAML CI/CD configuration in GitLab deployments. The expert mentions that a flaw of this nature can create a means for malicious hackers to steal sensitive information such as passwords and cloud service credentials: “Facilities that had a particular configuration to allow GitLab’s internal network requests were vulnerable to the SSRF attack, where an attacker could have sent a request to internal servers by jumping from GitLab’s public servers.
Internal servers are generally not exposed to the Internet, as they are only intended for internal use and may contain sensitive information such as passwords, API keys, and cloud service credentials. All of this sensitive data would have been vulnerable in a compromised deployment. The vulnerabilities were identified as CVE-2021-22175 and CVE-2021-22214.
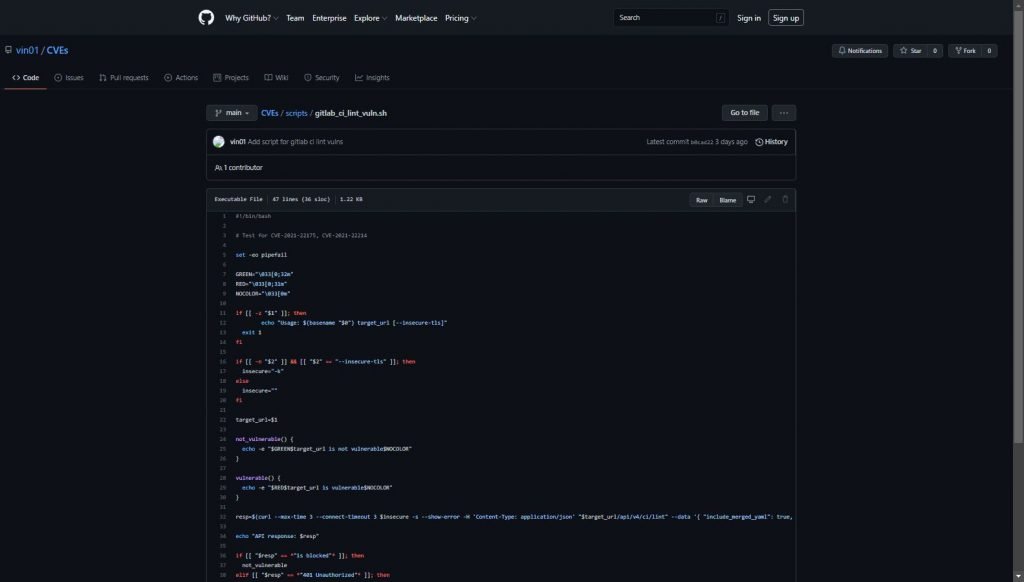
The researcher who initially reported the flaws also revealed a small script to test whether a GitLab server is vulnerable to this condition. The script is available on GitHub.
To learn more about information security risks, malware variants, vulnerabilities and information technologies, feel free to access the International Institute of Cyber Security (IICS) websites.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











