A complex cyberattack campaign against the Kenyan government led to improper approval for the construction of at least 18 buildings in the city of Nairobi. According to Mohamed Badi, director of Nairobi Metropolitan Services (NMS), the threat actors behind this incident acted in complicity with employees of this organization, which facilitated the illegitimate access.
The public official mentioned that some of the operators of this fraud have already been arrested, in addition to the fact that the authorities are already on the trail of the rest of the criminals: “This incident was the product of complex hacking techniques, which allowed unauthorized groups to obtain permits for construction activities.”
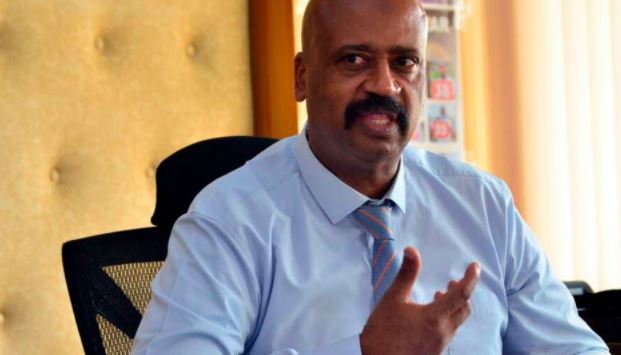
Badi went on to reaffirm that hackers are no strangers to the compromised systems, but had access with the collaboration of one or more internal accomplices: “We will not allow the construction of the buildings related to this incident to go ahead. We regret that the inhabitants in some areas have fallen into the trap of these criminals.”
It appears that the security weaknesses exploited by the hackers have already been addressed, so local authorities hope that no further exploitation attempts will occur, in addition to a specialized team conducting a deeper security audit: “We handed over the compromised system to the experts to investigate the situation. It took us almost two weeks to correct all the flaws,” Badi added.
The incident also led to the suspension of development plans in Nairobi due to the system’s commitment to generating Quick Response (QR) codes. These codes generate a unique identification to find all architectural plans approved so far by real estate authorities, eliminating the need for developers to submit hard copies of each plan.
To learn more about information security risks, malware variants, vulnerabilities and information technologies, feel free to access the International Institute of Cyber Security (IICS) websites.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











