Cybersecurity experts report the detection of a botnet allegedly operated from China, infecting around 100 thousand devices according to the figures collected until June 2021. According to Avast’s report, the malware of this botnet, known as DirtyMoe, PurpleFox or Perkiler was identified for the first time since the end of 2017.
The goal of the operators of this botnet is to infect thousands of Windows systems to mine cryptocurrencies (cryptojacking attack) without affected users detecting the infection, although experts mention that the botnet has also been used to launch denial of service (DoS) attacks. The operators deploy the malware via malicious emails and websites that host a toolkit identified as PurpleFox, which abuses some web browser-based flaws and gain access to the affected Windows systems.
This malicious tool had already been identified by the cybersecurity community, although its capabilities were never given much importance. However, according to the Avast report the botnet is growing at a steady rate, accumulating more than 100 thousand infected computers currently.
It is in 2021 when the highest point in the activity of DirtyMoe has been detected, whose operators have driven the massive deployment of malware, adding an SMB module capable of scanning the entire Internet and performing brute force attacks against exposed Windows systems.
The SMB module allows malware to explode in terms of infections, in what Avast described as a logarithmic scale, reaching more than 100 thousand infected systems during the first half of 2021 alone.
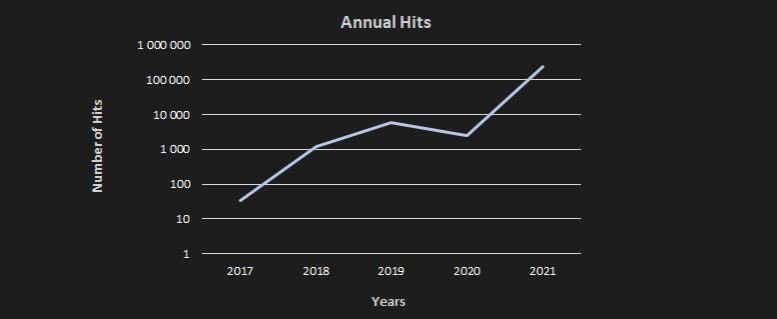
It should be noted that this is just an Avast estimate obtained from devices with their antivirus solution installed, so the number of DirtyMoe infections could be much higher. Another report, published by Chinese security firm Tencent also points to the rapid rise in DirtyMoe infections over the past few months, especially in Europe and Asia.
The threat is still active, although Avast is already preparing a report on the evolution and operations of malware, along with indicators of compromise (IOC) that administrators of affected systems will be able to identify a possible infection.
To learn more about information security risks, malware variants, vulnerabilities and information technologies, feel free to access the International Institute of Cyber Security (IICS) websites.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











