Just a few hours ago it was revealed that a JSON database with over 68 MB of data extracted from LinkedIn is available on a popular dark web hacking forum. The person responsible for the publication states that the database includes information about some business owners in the U.S., including full names, email addresses, work address and other details publicly available on most LinkedIn profiles.
It is true that these are not considered confidential records and that it is highly likely that the database will only include publicly available information. However, a detailed analysis of this data could be useful to many threat actors, including phishing campaign operators and ransomware hackers.
LinkedIn has already spoken out about it, posting a brief message ruling out treating this incident as a data breach: “Our security teams investigated a set of data allegedly extracted from LinkedIn for sale online. We want to make it clear that this is not a data breach and that our users’ information is completely secured.”
Still, the cybersecurity community continued to analyze the leak, discovering that the compromised files include professional records and some details such as:
- Full names
- Email addresses
- Locations
- LinkedIn summaries, some of which include other contact information
- Academic training data
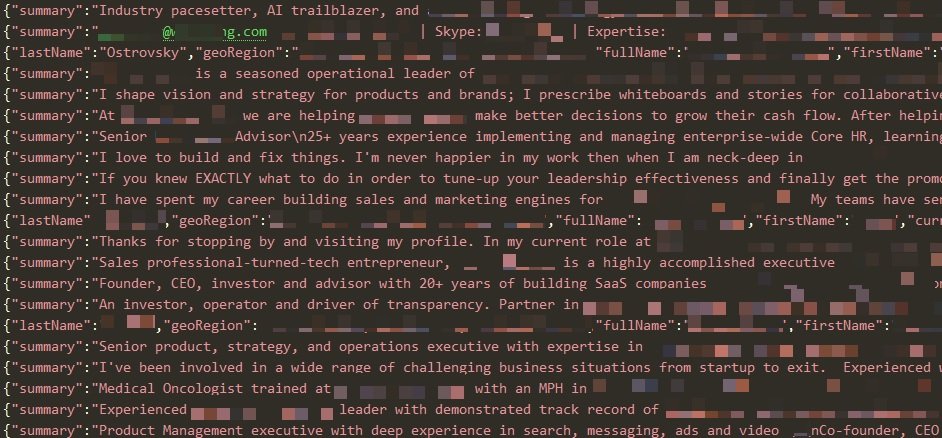
As mentioned above, the database is composed of records extracted from the profiles of more than 88,000 business owners in the U.S. However, the file appears to have just 6,500 unique email addresses, plus there appears to be no evidence of leaking sensitive data.
This is an example of a practice known as scraping, which consists of collecting information available only from public sources, including Facebook, Twitter, Instagram or LinkedIn profiles.
While virtually all tech companies have similar positions on this practice and consider it somewhat conventional, cybersecurity specialists say that data available from public sources can also be used by threat actors, so better mechanisms against this practice must be implemented.
To learn more about information security risks, malware variants, vulnerabilities and information technologies, feel free to access the International Institute of Cyber Security (IICS) websites.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











