Lenovo security teams announced the detection of three vulnerabilities affecting the BIOS of approximately 60 models of laptops and notebooks. In its notice, the company claims to be working to release BIOS updates for more than 32 ThinkPad models and expects to begin rolling out the patches on July 28.
The first of these flaws was tracked as CVE-2021-3452 and resides in the ThinkPad models, specifically in the system shutdown SMI callback function and could be exploited by a local threat actor to execute arbitrary code.
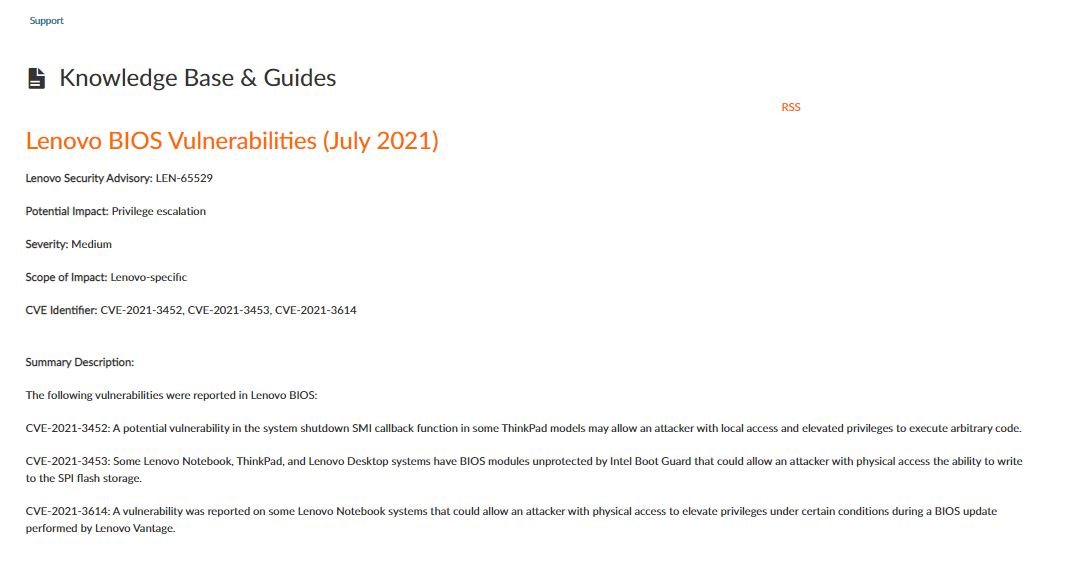
Moreover, five ThinkPad models that are not affected by this vulnerability are impacted by CVE-2021-3453, a bug that exists because BIOS modules are not protected by Intel Boot Guard. A threat actor with physical access to the affected devices could write to SPI flash storage.
Lenovo has already released multiple BIOS updates for the affected ThinkPad devices, though its security teams are still working on security patches for 13 vulnerable laptop models. The flaws that have not been addressed also affect the ideacentre series desktops, which could be updated until the end of September.
Finally, the third vulnerability was tracked as CVE-2021-3614 and affects only Lenovo laptop models. Exploiting this flaw could allow local malicious hackers to perform a privilege escalation attack under certain circumstances and during a BIOS update.
This flaw resides in at least 21 laptop models, although so far only updates have been released to address the flaws in two of these computers. Lenovo had announced the release of an update for a vulnerable third computer, although that update remains unavailable.
For security, users are advised to stay on top of any new updates released by Lenovo, as well as visit the company’s official platforms to find detailed information on these flaws.
To learn more about information security risks, malware variants, vulnerabilities and information technologies, feel free to access the International Institute of Cyber Security (IICS) websites.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











