French cybersecurity specialist Gilles Lionel reported the discovery of a serious vulnerability in the Windows operating system that would allow threat actors to arbitrarily authenticate to remote Windows servers in order to access NTLM authentication details or authentication certificates.
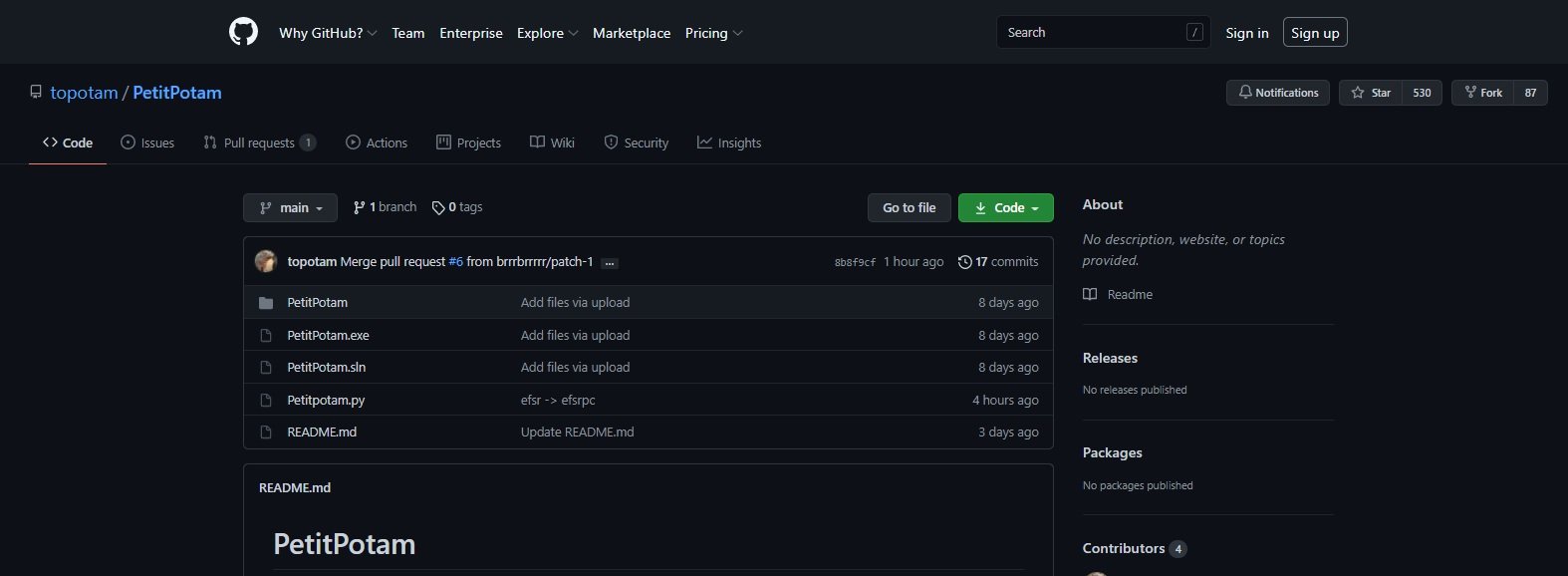
The flaw was dubbed “PetitPotam” and already has a proof of concept (PoC) whose code is available on GitHub from this weekend. The researcher points out that this problem arises when threat actors abuse MS-EFSRPC, a protocol employed by devices with Windows systems to perform operations with encrypted data stored on remote systems.
Using PoC code, attackers could send SMB requests to the affected interface, forcing the target system to initiate an authentication procedure that will result in the exposure of sensitive information. Threat actors can use this information as part of an NTLM relay attack to gain access to remote systems on the same internal network.
It is worth mentioning that this attack must be deployed locally and can be especially harmful to large corporate networks, in which threat actors can force domain controllers to remove hashing of their NTLM passwords, allowing the total compromise of the affected networks.
The researcher’s tests looked at Windows Server 2016 and 2019 systems; although Gilles believes it is highly feasible that this attack can affect most currently supported Windows Server versions.
In this regard, Microsoft published on its official platforms a series of measures to mitigate the risk of exploitation, although nothing was mentioned about a possible additional patch. This is the third high-profile Vulnerability related to Microsoft products reported in recent weeks, following the chaos generated by the PrintNightmare and SeriousSAM flaws; reports of these flaws being exploited in real-world scenarios continue to circulate, indicating that users do not always install critical patches released by tech companies, allowing threat actors to continue abusing some bugs that should already have been addressed by users.
To learn more about information security risks, malware variants, vulnerabilities and information technologies, feel free to access the International Institute of Cyber Security (IICS) websites.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











