Cybersecurity specialists detailed the finding of a severe vulnerability in WhatsApp whose exploitation would allow threat actors to access confidential information stored in the application’s memory. This platform, owned by Facebook, acknowledged and addressed the flaw in early 2021.
This flaw, discovered by Check Point Research experts was described as an out-of-bounds reading and writing error related to the image filter feature: “A successful attack would have required a complex process and a lot of user interaction, which certainly complicates its exploitation in real scenarios,” the report states.
The company notes that, until the time of its correction, no successful exploitation attempts or any malicious campaign related to this vulnerability were detected.
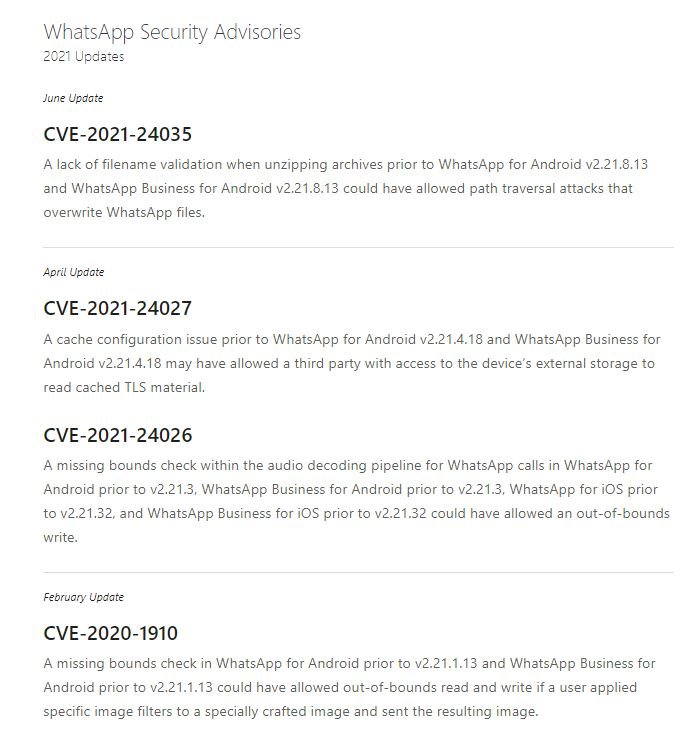
This flaw could have been triggered in case a user opened a malicious file with an image attached, to subsequently apply a filter to the image and then send it to the attacker. The vulnerability was detected in November 2020 and addressed in version v2.21.1.13, which adds two additional checks to the original image.
The report was taken seriously by WhatsApp, as more than 50 billion messages are sent daily through this platform, including some 4 billion photos: “The report was based on a detailed analysis of the way the company processes and sends images, including BMP files, GIF, JPEG and PNG,” the researchers note.
Applying filters to images on WhatsApp involves reading the contents of the file and manipulating the values of its pixels, as well as writing data to a new target image. According to experts, switching between various filters in specially designed GIF files causes the application to crash.
“After reverse engineering we found a memory corruption problem. Before continuing our investigation, we reported the issue to WhatsApp, which tracked the vulnerability as CVE-2020-1910 and determined that it was a heap-based out-of-bounds read/write error,” the report adds.
The flaw is caused because the application assumes that both the original image and the target image have the same dimensions. Therefore, an image created for malicious purposes and with a specific file size can lead to out-of-bounds memory access.
The flaw was fixed by having WhatsApp validate that the image format is equal to 1, which means that both the source and filter images must be in RGBA format. The new correction also validates the image size by checking the image dimensions.
To learn more about information security risks, malware variants, vulnerabilities and information technologies, feel free to access the International Institute of Cyber Security (IICS) websites.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











