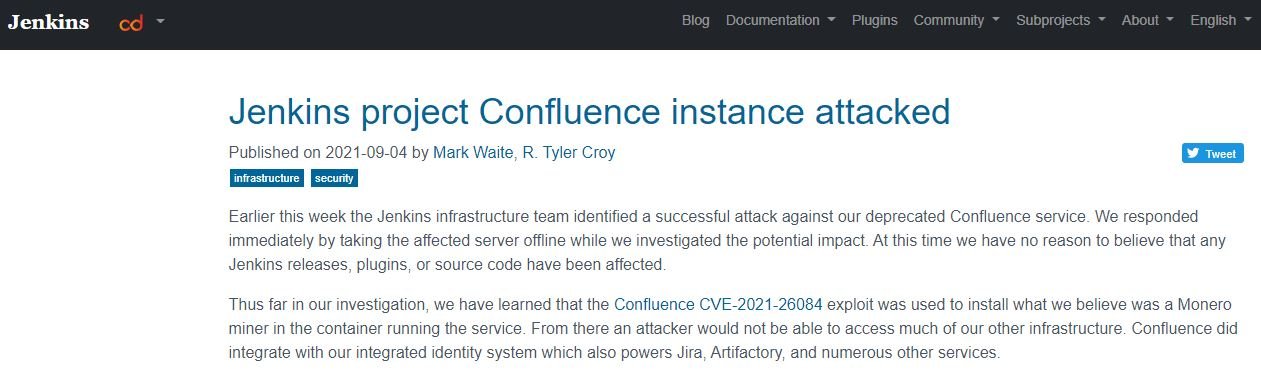
Jenkins security teams confirmed the detection of a successful cyberattack targeting Confluence, a service that has already reached the end of its useful life. According to the report, Jenkins responded immediately by disconnecting the attacked server and cutting off the spread of the infection, ensuring that hackers failed to access source code or more sensitive material.
During this attack, hackers would have exploited CVE-2021-26084, a severe vulnerability in Confluence that allowed software to be installed to mine the Monero cryptocurrency in the container running the affected service. Confluence integrated with our integrated identity system that also powers Jira, Artifactory, and many other services.
After containing the attack, Jenkins began taking the necessary steps to remove the infection and start a chain of trust with the developers. As part of these measures, passwords for all developer accounts were reset and an improved password reset system will be implemented to address future security incidents.
By this time, Jenkins’ infrastructure team has already permanently disabled the Confluence service, in addition to rotating privileged credentials and taking proactive steps to further reduce the scope of the attack: “We are working closely with our colleagues at the Linux Foundation and Continuous Delivery Foundation to ensure that infrastructure that is not directly managed by the Jenkins project is also analyzed,” added the experts.
In October 2019, confluence’s server became read-only and effectively wasted for daily use within the project. At that time, jenkins’ team began migrating documentation and change logs from the wiki to GitHub repositories. That migration has been ongoing, with hundreds of plugins and many other documentation pages moved from the wiki to GitHub repositories.
To learn more about information security risks, malware variants, vulnerabilities and information technologies, feel free to access the International Institute of Cyber Security (IICS) websites.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











