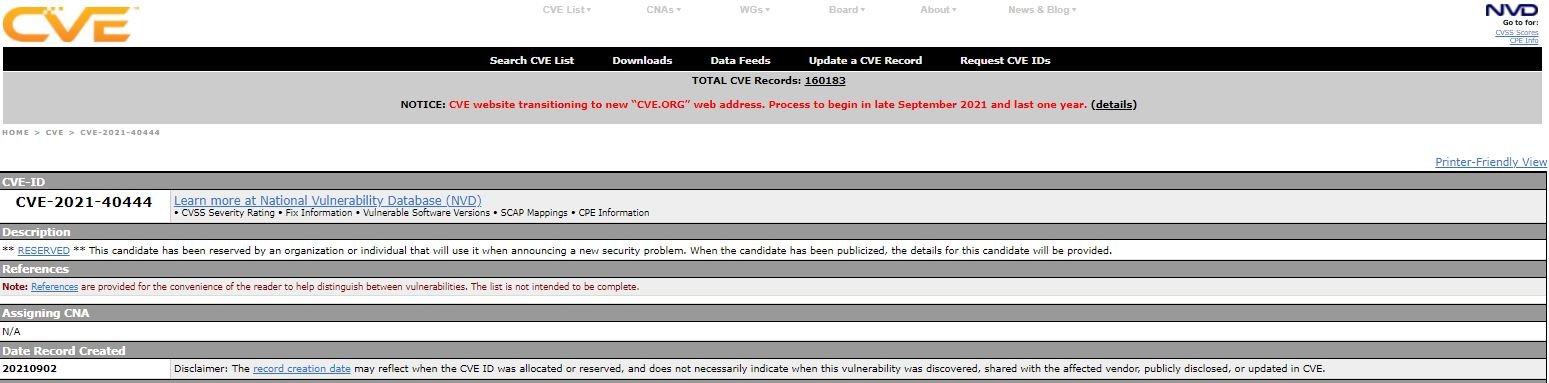
Microsoft security teams issued an alert to ask users of Windows systems to take appropriate measures to prevent the exploitation of a zero-day MSHTML vulnerability of remote code execution through malicious documents from the Microsoft Office suite. The flaw was tracked as CVE-2021-40444, although due to the latent risk of exploitation the company has not revealed further details about it.
According to the report, successful exploitation of the flaw would allow threat actors to create a malicious ActiveX control that would be employed by a Microsoft Office document hosting the browser’s rendering engine.
To complete the attack, malicious hackers would have to trick the target user into opening the infected document. In addition, users whose accounts are configured for least-privilege use might be less exposed to this attack variant.
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) also issued an alert about the vulnerability, recommending Windows users and system administrators implement some of the temporary fixes issued by Microsoft.

The investigation is still ongoing, so Microsoft could confirm that this risk goes beyond the potential infection of Office documents due to the use of MSHTML, predicts Jake Williams, security researcher at the firm BreachQuest: “If you have ever opened an application that knows its proxy settings without apparent explanation, it’s probably because of a bug in MSHTML. These types of safety flaws seem to have a very long lifespan,” adds the researcher.
Even if it were confirmed that the attack is limited to the use of Office documents, the mere existence of the risk has triggered multiple exploitation campaigns in real scenarios, making it urgent for potentially exposed organizations to implement some security measures.
Microsoft would issue a series of patches in the coming days, although their characteristics will depend on the findings of its research team. While this is happening, customers should check that their anti-malware products are kept up to date in case they don’t resort to automatic updates. On the other hand, enterprise customers should select detection build 1.349.22.0 in order to avoid the risk of exploitation, at least temporarily.
Other workarounds for the flaw include disabling any installation of ActiveX controls in Internet Explorer.
To learn more about information security risks, malware variants, vulnerabilities and information technologies, feel free to access the International Institute of Cyber Security (IICS) websites.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











