In its latest security alert, Google announced the release of fixes for 11 flaws in Chrome, including two zero-day vulnerabilities already exploited in the wild. Among all the reported flaws, those considered the most dangerous are CVE-2021-30632 and CVE-2021-30633.
The company’s statement reads: “Google is aware that exploits for the aforementioned flaws exist in nature. These reports were sent to our security teams on September 8 by anonymous investigators.”
Below is a list of all reported flaws:
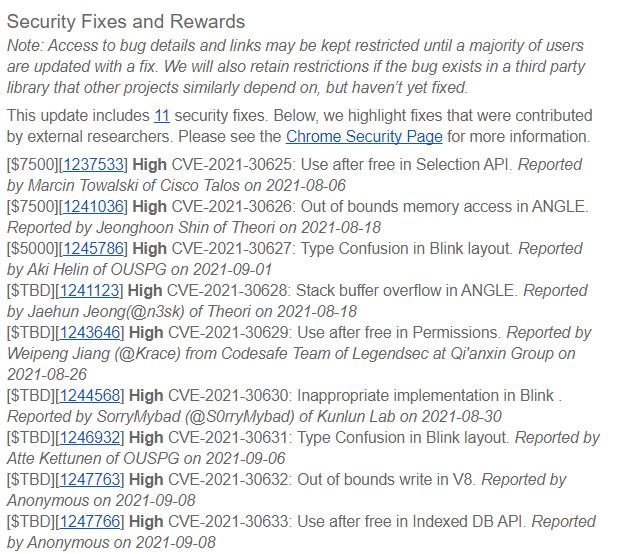
While CVE-2021-30632 was described as an out-of-bounds write flaw in the V8 engine, CVE-2021-30633 is a use-after-free error in the indexed database API. The tech giant claims that the updates will be implemented in the coming days as part of update 93.0.4577.82, compatible with Windows, Mac and Linux systems.
As some users will recall, V8 is an open source engine for JavaScript and WebAssembly, created by Google for your web browser.
Cybersecurity specialists emphasize that this is the tenth zero-day flaw in Chrome successfully exploited so far in 2021. Kevin Dunne, a specialist at the firm Pathlock, believes this is due to the wide availability of sensitive information that hackers can find in a web browser: “These attacks allow threat actors to gain access to millions of devices regardless of the operating system.”
For users, it is important that Google and other browser developers monitor the presence of these security flaws in real-world scenarios, as timely detection of an exploit could prevent millions of attacks: “It’s natural to expect the finding of zero-day exploits, so we’re left to trust that companies will be able to address these flaws before their exploitation skyrockets.”, concludes Dunne.
When the fix of a zero-day vulnerability for web browsers is announced, security incidents related to the exploitation of these flaws usually increase, so it is essential that Chrome users allow the update of their implementations to enjoy as safe browsing as possible.
To learn more about information security risks, malware variants, vulnerabilities and information technologies, feel free to access the International Institute of Cyber Security (IICS) websites.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











