Cybersecurity specialists report the detection of a design error in an important function of the Microsoft Exchange email server that could be abused by threat actors in order to collect Windows domains and application credentials from millions of users.
Amit Serper, the specialist in charge of the finding, mentions that the error lies in the Microsoft Autodiscover protocol, a feature of email servers in Exchange that allows email clients to automatically detect a server, provide credentials and receive the corresponding configurations.
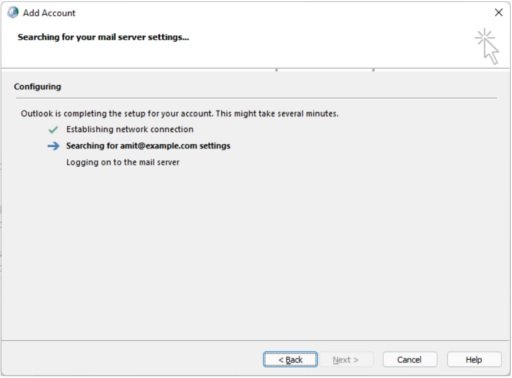
This protocol is a fundamental element for Exchange email servers, as it allows administrators to ensure that clients use configurations such as SMTP, IMAP, LDAP and WebDAV, among others. Accessing these automatic settings would allow email clients to ping a set of default URLs, all derived from the user’s email domain:
- https://autodiscover.example.com/autodiscover/autodiscover.xml
- http://autodiscover.example.com/autodiscover/autodiscover.xml
- https://example.com/autodiscover/autodiscover.xml
- http://example.com/autodiscover/autodiscover.xml
The expert mentions that this automatic detection mechanism used a back-off procedure in case of not finding the endpoint of the Exchange server in a first attempt: “This mechanism is the culprit of this leak because it always tries to solve the automatic detection part of the domain and will always try to fail, so to speak,” says Serper.
The result of the next attempt to create an autodiscover URL would be: http://autodiscover.com/autodiscover/autodiscover.xml, which means that the owner of autodiscover.com will receive all requests that cannot reach the original domain.
For his research, the expert registered a number of top-level domains based on automatic detection that were still available online, including:
- Autodiscover.com.br (Brazil)
- Autodiscover.com.cn (China)
- Autodiscover.com.co (Columbia)
- Autodiscover.es (Spain)
- Autodiscover.fr (France)
- Autodiscover.in (India)
- Autodiscover.it (Italy)
- Autodiscover.sg (Singapore)
- Autodiscover.uk (United Kingdom)
- Autodiscover.xyz
- Autodiscover.online
Using honeypots to measure the scale of the problem, Serper found that vulnerable servers received hundreds of requests, involving thousands of user credentials trying to set up their email clients.
The researcher found credentials associated with all kinds of organizations, including food manufacturers, financial institutions, critical infrastructure and other public organizations. Microsoft acknowledged the report and said steps are being taken to detect the exact causes of the flaw before incidents of malicious exploitation are known.
To learn more about information security risks, malware variants, vulnerabilities and information technologies, feel free to access the International Institute of Cyber Security (IICS) websites.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











