A recent research published by Positive Technologies points to the discovery of two vulnerabilities in Wincor Cineo ATMs, developed by the renowned ATM manufacturer Diebold Nixdorf, established in the U.S. According to the report, successful exploitation of the vulnerabilities would allow attackers to make the machine throw cash arbitrarily using only one command.
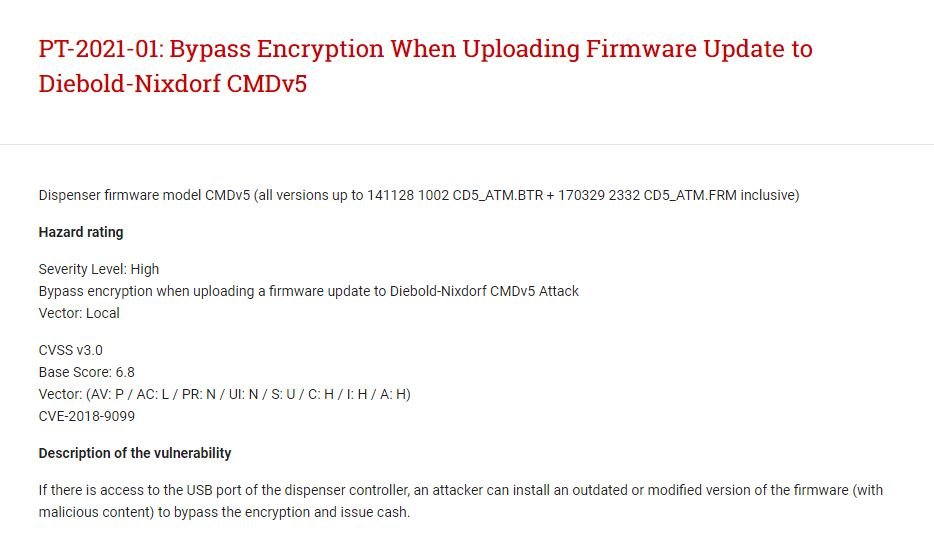
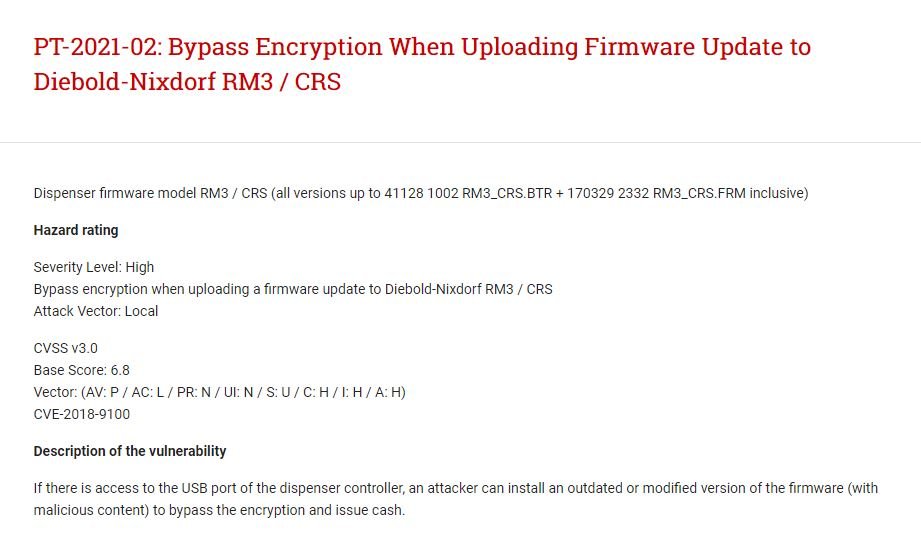
The researchers showed that the protections against black box attacks built into these ATMs can be bypassed by simply replacing the firmware of the cash dispenser controller. As some users may already know, these security mechanisms consist of applying end-to-end encryption to the controller traffic.
Apparently, the attack can be successfully completed in a matter of minutes if threat actors have access to the USB port of the compromised machine. The attack described by experts and carried out in a secure environment is divided into three distinct stages:
- Connecting a third-party device to an ATM
- Loading an outdated and vulnerable firmware version
- Exploitation of known vulnerabilities to access machine content
The vulnerabilities, tracked as CVE-2018-9100 and CVE-2018-9099, reside in Wincor Cineo ATMs with RM3/CRS and CMD v5 cash dispensers, respectively. Organizations that have these machines must address the failures by applying the corresponding firmware updates, or by requesting the manufacturer that the machine be replaced with a newer version.
Both flaws were discovered and presented to Diebold Nixdorf more than three years ago and have finally been fixed, so the researchers decided to share their findings with the cybersecurity community. This research will also be presented at the security conference Hardwear.io, to be held in the Netherlands in a few days’ time.
This isn’t the first time Positive Technologies researchers have found critical ATM failures. In 2018, a team of experts collaborated with manufacturer NCR to eliminate a similar flaw in its ATMs, which was corrected before it could be exploited in real scenarios.
To learn more about information security risks, malware variants, vulnerabilities and information technologies, feel free to access the International Institute of Cyber Security (IICS) websites.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.