Cybersecurity specialists from Positive Technologies report the detection of three critical vulnerabilities in the Adaptive Security Appliance (ASA) and Firepower Threat Defense (FTD) firewalls, developed by Cisco and whose exploitation would allow threat actors to deploy denial of service (DoS) attacks, among other risk scenarios. According to the report, the flaws received scores of 8.6/10 according to the Common Vulnerability Scoring System (CVSS), so users of vulnerable deployments are recommended to update as soon as possible.
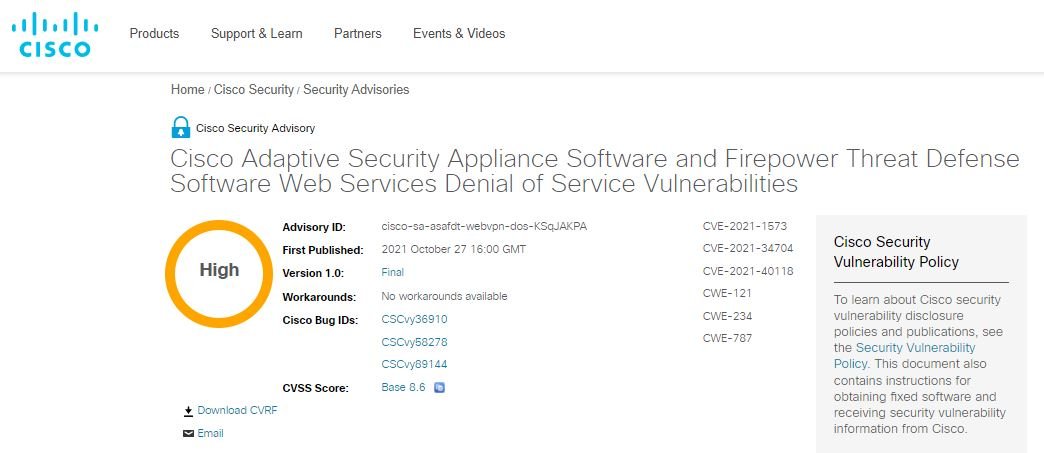
The flaws were tracked as CVE-2021-1573, CVE-2021-34704 and CVE-2021-40118, and their reports were attributed to various experts, including Cisco’s security teams.
As some users will recall, Cisco is a market leader in enterprise firewall and other security solutions. According to figures from the company itself, currently more than 1 million Cisco devices operate in large, medium and small firms around the world.
On the worst of these flaws, Nikita Abramov, a researcher at Positive Technologies, says: “If a hacker manages to disrupt the operation of the affected solutions, the affected organizations would be left without firewall remote access via VPN. In addition, the absence of a firewall will greatly reduce defenses against security threats.”
The expert adds that threat actors do not need high privileges on the vulnerable system or special access to exploit this error, since it is enough to form a simple request in which one of the parties will be of a different size than expected by the target device. A more detailed analysis of the request will cause a buffer overflow and the system will shut down, forcing a restart.
Cisco released a detailed report to address the flaws found, so administrators are encouraged to stick to these security recommendations, which include official updates. At the moment there are no known alternative solutions to these flaws, so it is best to update as soon as possible.
The company adds that so far no attempts to actively exploit these flaws or the existence of a malware variant associated with the attack have been detected.
To learn more about information security risks, malware variants, vulnerabilities and information technologies, feel free to access the International Institute of Cyber Security (IICS) websites.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











