A few days ago Panasonic confirmed a data breach incident that resulted in the compromise of a file server that could have stored sensitive information. In this regard, the Japanese firm only confirmed that the incident had been detected on November 11, although they refused to add more information because the investigation was still ongoing.
In this regard, the Japanese website NHK published a report in which they claim that the compromised server stored confidential information about business partners, employees and technology developed by Panasonic. While the company shut down unauthorized access when the incident was detected, its security teams are still trying to determine if the exposed information was somehow compromised.
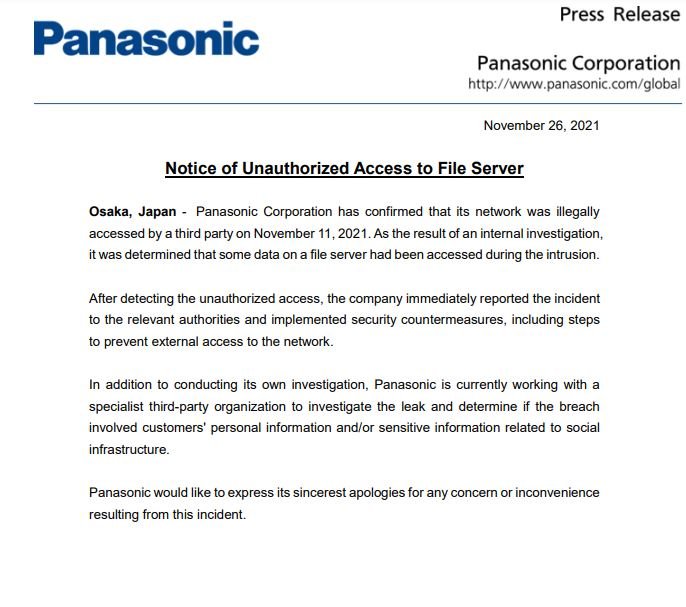
Panasonic ordered an investigation by an outside cybersecurity firm, which would allow determining determine the scope of the incident and know exactly which records could be compromised, so more information could eventually appear. Although Panasonic has not confirmed it, it is mentioned that unknown actors accessed the server on multiple occasions between June and November; the company did not deny NHK’s report, so it is believed that these researchers’ estimates are likely to be legitimate.
This incident was detected just a year after Panasonic’s division in India confirmed that its information systems were compromised by unidentified threat actors, who managed to extract confidential information and tried to extort money from the company in exchange for not disclosing this data.
In total, the attackers leaked 4GB of data, including financial records, login credentials and email addresses. Although Panasonic India confirmed the incident, the company never found evidence of malicious use of these records, so the case was closed.
To learn more about information security risks, malware variants, vulnerabilities and information technologies, feel free to access the International Institute of Cyber Security (IICS) websites.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











