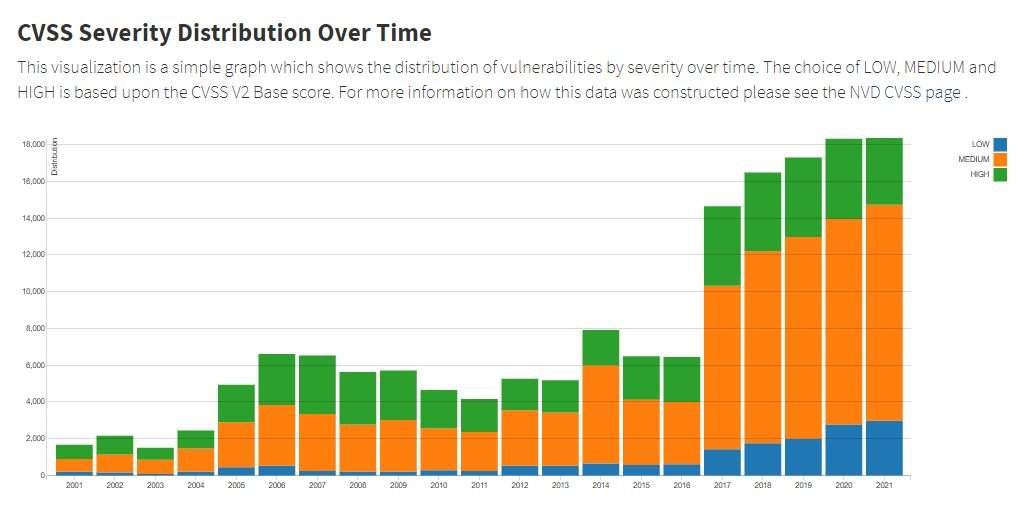
A report from the National Institute of Standards and Technology (NIST) details the number of vulnerabilities found in 2021, which amounts to 18,378 flaws, thus breaking the record set the previous year for the fifth consecutive time.
Something remarkable is that experts point out that the number of critical flaws decreased, going from 4,381 critical vulnerabilities found in 2020 to 3,646 during the last months.
Opinions on this report are diverse, as there is some confusion about the critical vulnerabilities gathered in the report, while some researchers believe that the NIST report fully matches the behavior of the vulnerabilities during 2021.
In this regard, cybersecurity specialist Casey Ellis believes that vulnerability detection is inherent in software development, so it is normal that more and more errors are found every year: “The more software is created, the more critical vulnerabilities will exist,” adds Ellis.
The expert also mentions that lower-impact security issues are relatively easy to find, so the frequency with which they are reported is considerable. Finding a severe fault is a more complicated task, although its correction may be a more accelerated process due to the risks inherent in its exploitation: “They are often given priority for root cause analysis and pattern evasion in the future, and therefore can often be smaller in number,” adds the expert.
On the other hand, cybersecurity specialist Pravin Madhani, CEO of K2 Cyber Security mentions that the lower detection of vulnerabilities is due to the advancement in coding practices implemented by software developers, a practice that has increasingly focused on the integrity of systems.
Experts also point out that the increase in remote work due to the COVID-19 pandemic was a factor that undoubtedly contributed to the increase in the detection of security vulnerabilities, as most public and private organizations began to adopt the use of remote access tools and other software variants to allow their employees to work from home.
NIST concludes that security bugs are something typical of technological development, so it remains for developers and researchers to continue working to avoid the exploitation of the most dangerous security flaws, which will inevitably continue to appear.
To learn more about information security risks, malware variants, vulnerabilities and information technologies, feel free to access the International Institute of Cyber Security (IICS) websites.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











