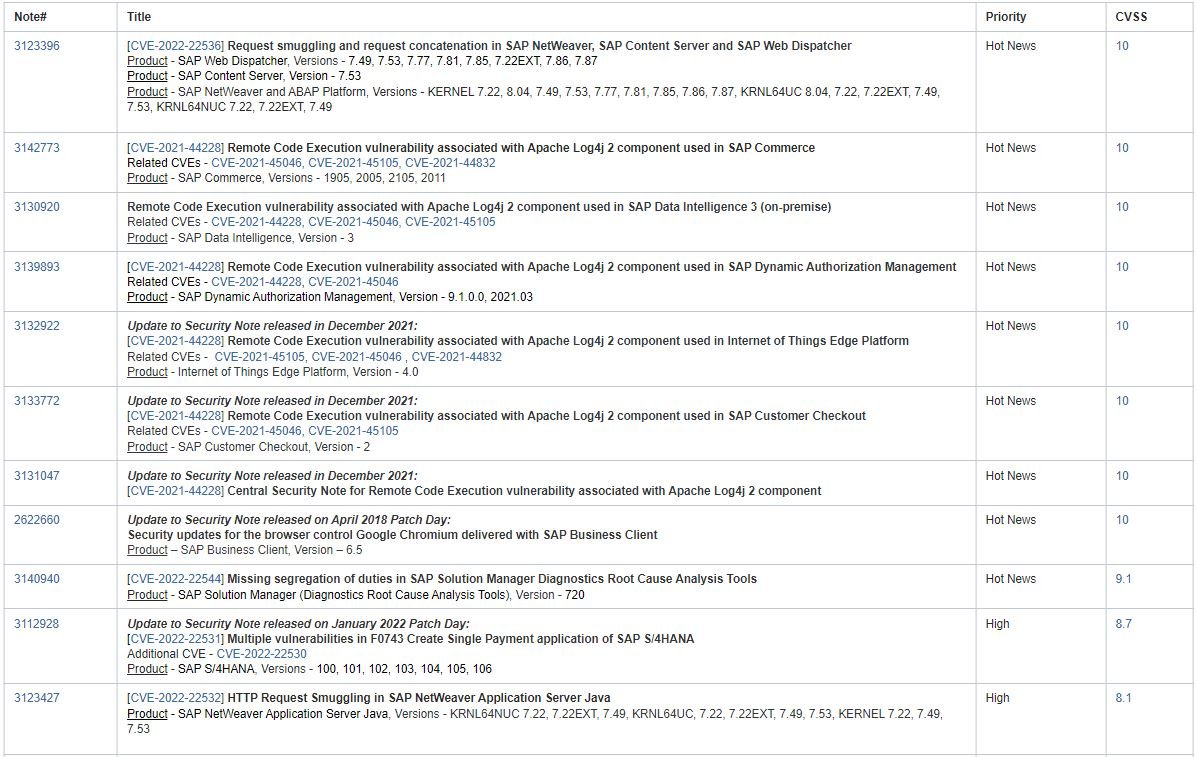
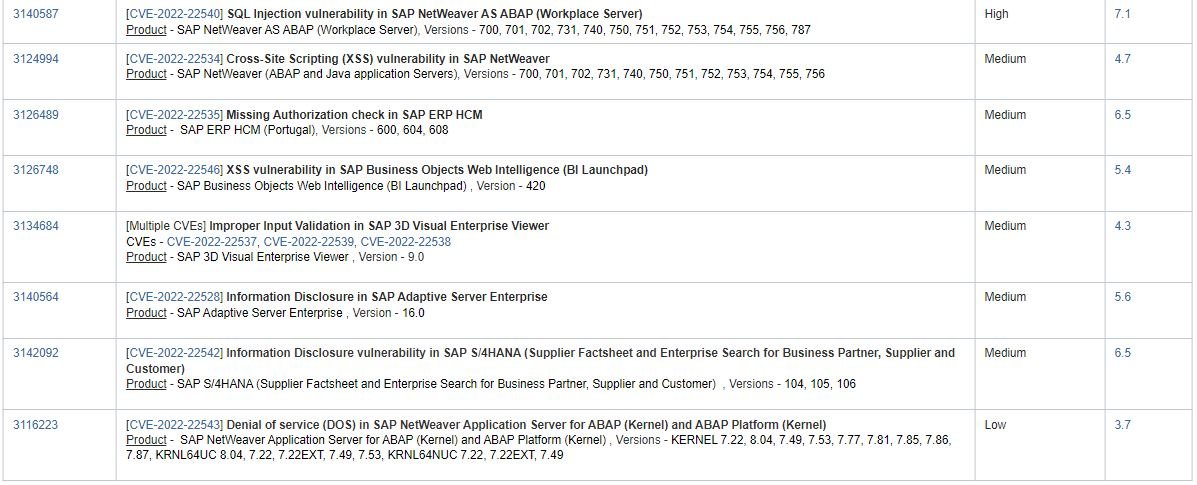
SAP security teams confirmed the patching of 19 vulnerabilities affecting various products, among which three critical flaws according to the Common Vulnerability Scoring System (CVSS) stand out. The flaws were reported by researchers at security firm Onapsis.
This set of flaws, dubbed as ICMAD, resides in SAP Internet Communication Manager (ICM), a core component of multiple SAP applications. This set of vulnerabilities would allow threat actors to execute critical attacks against SAP users, compromise the sensitive information of thousands of organizations, and take control of SAP products without updating.
This component enables HTTP(S) communications in SAP systems and, as it is exposed to the Internet and untrusted networks by design, security flaws affecting this component present an increased risk to affected users.
The researchers mention that an attacker could steal all of the victim’s sessions and credentials in plain text and modify the behavior of applications. In addition, exploiting faults could be a trivial process, as no authentication or preconditions are required in the system and the payload can be delivered over HTTPS.
Both SAP and the U.S. Cybersecurity and Infrastructure Security Agency (CISA) issued security alerts asking customers to deploy the patches required to mitigate the risk of exploitation: “Failures can be exploited over the Internet and without the use of authentication, which makes this a critical issue,” the Agency notes.
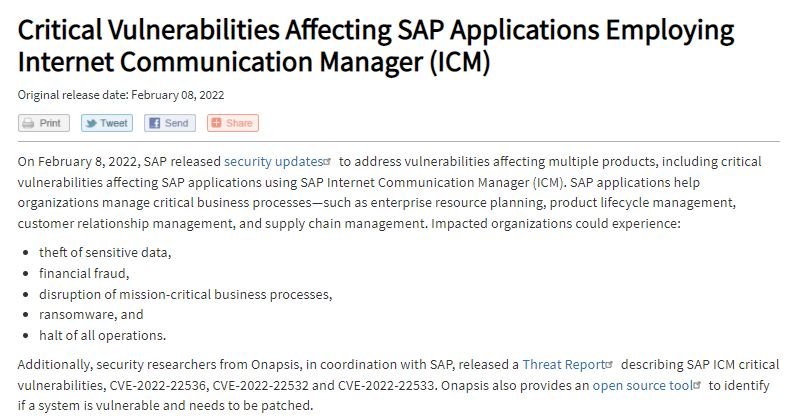
Onapsis has submitted similar reports before. These reports agree that an attacker could send malicious payloads exploiting this and other hard-to-detect HTTP smuggling techniques; flaws can be exploited remotely and without authentication, so mechanisms such as multi-factor authentication are not helpful against this attack.
The good news is that SAP ensures that no security incidents related to the exploitation of these flaws have been detected. Still, the company recommends users of affected deployments fix them as soon as possible, as SAP applications are often frequent targets of the world’s most dangerous hacking groups.
To learn more about information security risks, malware variants, vulnerabilities and information technologies, feel free to access the International Institute of Cyber Security (IICS) websites.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











